AT A GLANCE
Network analysis is a data visualization and analytical technique that maps financial relationships between accounts, entities, and transactions to uncover hidden money laundering patterns. By representing accounts as nodes and transactions as connecting links, investigators can spot suspicious activity like circular flows, shell company networks, and layering schemes that traditional transaction monitoring might miss. This technology has become essential for modern AML compliance programs because it provides the context needed to distinguish between legitimate complex transactions and sophisticated laundering operations.
What Is Network Analysis and Why Does It Matter for AML Investigations?
Network analysis is the study of how entities relate to and interact with one another within a connected system. In anti-money laundering contexts, these entities include bank accounts, individual customers, corporations, transactions, and financial institutions themselves.
At its foundation, network analysis transforms raw financial data into visual representations that human investigators can quickly understand. Each account holder or entity becomes a "node" in the network, while transactions, contracts, or other financial relationships become "edges" or "links" connecting those nodes. When plotted together, these elements form a web or graph that reveals patterns invisible in spreadsheet data.
The financial system processes billions of transactions daily across multiple currencies, countries, and institutions. Money launderers deliberately exploit this complexity, hiding illicit funds within the legitimate flow of global commerce. Traditional rule-based transaction monitoring systems examine individual transactions in isolation, which makes it difficult to detect sophisticated schemes that only become apparent when viewed holistically.
Network analysis addresses this limitation by mapping entire transaction ecosystems. Investigators can identify clusters of accounts that repeatedly transact despite having no legitimate business relationship, trace funds flowing through multiple intermediary accounts to obscure their origin, detect shell companies sharing directors or addresses that suggest coordinated activity, and spot sudden pattern changes that indicate suspicious behavior.
Modern financial institutions face an ongoing challenge: money launderers continuously evolve their tactics, while compliance teams must reduce false positives and focus investigative resources efficiently. Network analysis provides context that helps distinguish between genuinely suspicious activity and complex but legitimate business operations.
How Do Investigators Use Network Analysis to Detect Money Laundering?
Investigators apply network analysis throughout the AML investigation lifecycle, from initial detection through case building for law enforcement referrals.
Identifying Suspicious Transaction Patterns
Money launderers use predictable patterns designed to confuse automated systems—rapid high-volume transactions, circular money flows, structured deposits below reporting thresholds, and dynamic risk scoring evasion tactics. Network analysis visualizes these patterns clearly, even when each individual transaction appears innocuous.
For example, a launderer might split $100,000 into 20 separate $5,000 deposits across different accounts to avoid a $10,000 reporting requirement. In a transaction list, these appear unrelated. In a network visualization, the pattern becomes immediately obvious—multiple nodes sending similar amounts to a central node within a compressed timeframe.
Unraveling Complex Laundering Schemes
Sophisticated laundering operations involve multiple layers spanning numerous banks, countries, currencies, and legal entities. Network analysis systematically dissects these layers, providing investigators a roadmap showing exactly how money moved, who controlled it at each stage, and where potential vulnerabilities exist in the laundering chain.
Detecting Shell Companies and Phantom Entities
A common laundering tactic involves routing funds through shell companies—legal entities with no real business operations. Through network analysis, investigators identify entities displaying unusual characteristics: high transaction volumes despite no apparent business activity, multiple companies sharing the same registered address, or entities with identical directors suggesting coordinated control.
Enhanced Customer Due Diligence
Customer due diligence requires understanding not just who your customer is, but also who they're connected to. Network analysis maps a customer's entire financial ecosystem—their business associates, affiliated entities, transaction counterparties, and beneficial owners. This reveals hidden risks, such as a customer's proximity to sanctioned individuals or connections to entities in high-risk jurisdictions.
What Are the Key Components of Network Analysis?
Understanding network analysis requires familiarity with its fundamental building blocks.
Nodes: The Entities in Your Network
Nodes represent individual entities within the financial ecosystem—a customer account, a corporation, a beneficial owner, or a bank. Each node can have attributes like account balance, country of registration, risk rating, or transaction history that help investigators quickly assess whether it warrants scrutiny.
Edges: The Connections Between Entities
Edges represent relationships or interactions between nodes. In financial networks, an edge typically represents a transaction, but can also represent corporate relationships, shared attributes, or contractual arrangements. Edges have attributes such as transaction amount, date, currency, or frequency that provide critical context for evaluating whether a connection is suspicious.
Network Attributes: The Bigger Picture
Beyond individual nodes and edges, the network itself has characteristics that reveal patterns. Network density measures how interconnected entities are—a very dense cluster might indicate a coordinated group. Centrality measures identify which nodes are most influential. Path analysis shows the routes money takes through the system.
Which Graph Analysis Techniques Work Best for AML Investigations?
Network analysis draws from mathematics, computer science, and social sciences, each contributing techniques that illuminate different aspects of financial crime.
Graph Theory Fundamentals
Graph theory provides the foundation for most network analysis. In AML contexts, graph-based techniques identify central nodes that might represent key players in laundering operations, detect communities or clusters revealing groups of accounts frequently transacting together, and measure network density to distinguish between tight-knit laundering schemes and legitimate business relationships.
Social Network Analysis in Finance
Betweenness centrality measures how often an entity acts as a bridge on the shortest path between two other entities. High betweenness centrality suggests the entity serves as a critical intermediary—in money laundering, these are often accounts that funds must pass through to reach their destination.
Eigenvector centrality identifies influential nodes based not just on how many connections they have, but on the quality of those connections. A node connected to many other well-connected nodes suggests it's part of an important subnetwork.
Temporal Analysis: Tracking Changes Over Time
Financial transactions occur in sequences, and timing matters. Temporal analysis examines the time dimension to understand laundering behaviors. Sequence pattern analysis reveals the order in which transactions occur, exposing multi-step laundering processes. Timing anomaly detection identifies transactions occurring at unusual hours or in rapid succession to confuse monitoring systems.
Layered Analysis for Multi-Dimensional Transactions
Money laundering often involves different transaction types—wire transfers, cash deposits, crypto and stablecoin. Investigators separate transaction types into distinct layers, analyze each for suspicious patterns, then integrate insights to understand the comprehensive structure of potentially laundered funds.
Geospatial Analysis
Mapping transactions geographically helps investigators identify high-risk zones, detect anomalous international transfers where funds route through countries with weak financial regulations, and spot inconsistencies between claimed business locations and actual transaction patterns.
Machine Learning Integration
Modern network analysis incorporates machine learning algorithms to predict potential suspicious activities based on historical patterns, cluster similar transaction behaviors to identify new laundering techniques, and continuously learn from investigator feedback to improve accuracy.
How Do Anti-Fraud Investigators Visualize Transaction Flows?
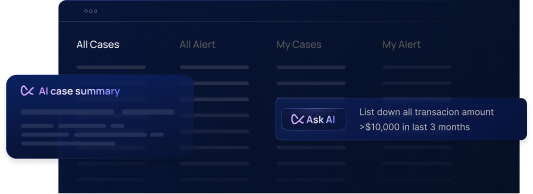
Visualization transforms complex transaction data into comprehensible formats that support rapid analysis. Modern AML platforms generate network graphs displaying entities as nodes with transactions as connecting lines, timeline visualizations showing transaction sequences chronologically, heat maps highlighting concentration areas, and geographic maps showing physical locations where transactions originate and terminate.
The most effective visualizations are interactive. Investigators can click on nodes to see detailed attributes, filter networks to show only certain transaction types, expand or collapse clusters to manage complexity, and highlight specific paths to trace fund flows from source to destination.
What Are the Main Challenges in Network Analysis for AML?
Data Volume and Complexity
Global financial institutions process millions of transactions daily across multiple currencies and time zones. The sheer volume strains even advanced systems, particularly when institutions need real-time analysis and watchlist screening to catch laundering as it happens.
Data Quality and Consistency
Network analysis is only as good as the underlying data. Missing information, clerical errors, inconsistent naming conventions, and outdated records skew results. Financial institutions must invest heavily in data governance, cleansing, and standardization.
Evolving Laundering Techniques
Money launderers adapt continuously. As detection methods improve, criminals develop new tactics. Network analysis systems require constant refinement—updating algorithms and adjusting detection models based on emerging threat intelligence.
False Positives
Identifying suspicious patterns doesn't guarantee actual illicit activity. Legitimate transactions can sometimes resemble laundering. False positives waste investigative resources and can damage customer relationships.
Privacy and Regulatory Compliance
Network analysis processes vast amounts of personal and transactional data, raising privacy concerns. Data protection regulations vary significantly across jurisdictions—what's acceptable in one country might violate regulations in another.
What Are Best Practices for Implementing Network Analysis in AML Programs?
Ensure Data Integrity
Conduct regular data audits to identify and correct inconsistencies. Establish data governance frameworks that define standards for data entry and quality control. Work with reputable data providers to supplement internal data with external intelligence.
Invest in Training and Skill Development
Host regular workshops updating investigative teams on evolving laundering tactics and network analysis techniques. Collaborate with experts in graph theory and data science to ensure your team remains at the cutting edge.
Continuously Refine Detection Models
Implement iterative testing and refinement of detection algorithms to reduce false positives and adapt to emerging threats. Create feedback loops where insights from concluded investigations inform and enhance detection models.
Integrate with Complementary Tools
Combine network analysis with machine learning-based anomaly detection, rule-based systems for known typology detection, natural language processing to analyze unstructured data, and case management systems to track investigations from detection through resolution.
Enable Real-Time Monitoring
Implement continuous surveillance systems that monitor transaction networks in real-time rather than batch processing overnight. Configure customizable alert systems based on your institution's risk appetite and thresholds.
Frequently Asked Questions About Network Analysis in AML
How does network analysis differ from traditional transaction monitoring?
Traditional transaction monitoring examines individual transactions in isolation against predefined rules. Network analysis examines relationships and patterns across multiple transactions and entities, providing context about how accounts and people are connected. While transaction monitoring might flag a single large wire transfer, network analysis reveals that the transfer is part of a circular flow involving five shell companies.
Can network analysis detect new money laundering techniques that haven't been seen before?
Yes, when combined with machine learning. Network analysis with unsupervised machine learning can identify anomalies—unusual patterns that deviate from normal behavior even if they don't match any predefined rule. However, it also generates false positives when legitimate but unusual activity occurs, which is why human expertise remains essential.
How long does it take to implement network analysis in an AML program?
Small to medium institutions might implement a basic network analysis capability in 6-12 months, while large global institutions often require 18-36 months for comprehensive implementation. The process includes data integration, tool selection, staff training, process development, pilot testing, and full rollout.
Do privacy regulations like GDPR conflict with network analysis for AML?
Not necessarily. GDPR and similar regulations permit processing of personal data for preventing financial crime, provided institutions implement appropriate safeguards including data minimization, purpose limitation, security measures, transparency, and data retention limits.
What skills do AML investigators need to use network analysis effectively?
Effective investigators need understanding of money laundering typologies, knowledge of financial products and transaction flows, data analysis skills, graph theory basics, critical thinking to distinguish between suspicious and legitimate complexity, and communication skills to explain complex findings.
Conclusion: Network Analysis as a Strategic Imperative for Modern AML
The global financial system faces an ongoing challenge from sophisticated criminal organizations that exploit complexity to disguise illicit funds. Traditional transaction monitoring approaches remain necessary but insufficient for detecting modern laundering schemes.
Network analysis represents a fundamental shift in how financial institutions approach AML compliance solutions, strengthened by AI forensics. By mapping the complex web of relationships between accounts, entities, and transactions, it provides the context needed to distinguish between genuinely suspicious activity and complex but legitimate business operations.
Success with network analysis requires more than just technology implementation. It demands high-quality data, well-trained investigators, refined processes, and strong governance frameworks. As regulatory expectations increase and the sophistication of financial crime grows, network analysis has moved from a nice-to-have capability to a strategic imperative for any institution serious about protecting the integrity of the financial system.




.svg)






.webp)