AT A GLANCE
Investigating suspicious transactions involves identifying red flags through monitoring tools, conducting thorough analysis of transaction patterns and customer behavior, documenting findings, and filing Suspicious Activity Reports (SARs) when warranted. Financial institutions must follow a systematic process combining technology with human expertise to detect money laundering, fraud, and other financial crimes while maintaining regulatory compliance.
What Is a Suspicious Transaction?
A suspicious transaction is any financial activity that deviates from expected patterns or suggests potential involvement in money laundering, fraud, or other financial crimes. These transactions aren't inherently illegal, but they warrant closer examination due to inconsistencies with normal customer behavior.
What makes them suspicious is context—how they differ from what's expected based on the customer's financial habits, business activities, or risk scoring. Some lack clear economic purpose, appear overly complex, or involve parties difficult to identify.
Key point: Suspicion doesn't equal proof of wrongdoing. These are signals requiring investigation, not automatic evidence of criminal activity.
How to Identify Suspicious Transactions?
Identifying suspicious transactions requires watching for specific red flags indicating potential money laundering, fraud, or other financial crimes.
Unusual Transaction Size or Frequency - Transactions significantly larger or more frequent than the customer's typical activity signal suspicious behavior. A customer processing $500 weekly who suddenly transfers $50,000 warrants investigation.
Geographic Anomalies - Transactions involving countries not associated with the customer's business or appearing on FATF watchlists raise red flags, particularly when lacking clear business justification.
Inconsistent Transactions - Transactions misaligned with stated business purpose, occupation, or known income sources require scrutiny. Examples include college students receiving regular $25,000 wire transfers or restaurants making frequent tech company payments.
Complex or Unusual Patterns - Unnecessarily complicated structures suggest attempts to obscure fund origins or destinations, including rapid movement through multiple accounts, shell companies without clear purpose, or structured deposits avoiding reporting thresholds.
Anonymous Transactions - Heavy use of anonymous payment processors, privacy coins, minimal-verification processors, or incomplete customer information often facilitate financial crime.
Practical tip: Create baseline profiles for each customer during their first 90 days. Flag deviations automatically, but investigate context before concluding suspicion.
What Tools Help Detect Suspicious Payment Activity?
Financial institutions rely on specialized transaction monitoring tools combining automated detection with human oversight to identify suspicious payment activity in real time.
Automated Transaction Monitoring Systems
These systems analyze every transaction against hundreds of risk rules and customer behavior patterns, flagging anomalies instantly. Modern systems use machine learning to detect emerging fraud typologies while reducing false positives.
Behavioral Analytics Platforms
These tools establish normal behavior baselines for each customer and identify deviations indicating potential fraud. They track changes in transaction timing, amounts, frequencies, and geographic patterns, excelling at detecting account takeover and gradual escalations in suspicious activity.
Link Analysis Tools
These platforms map relationships between customers, accounts, and transactions to uncover hidden connections. They reveal money laundering networks, identify beneficial owners behind shell companies, and trace fund flows through multiple intermediaries.
Watchlist Screening Solutions
These systems continuously screen customers and transactions against sanctions lists, PEP databases, adverse media, and law enforcement watchlists, providing real-time alerts when matches occur.
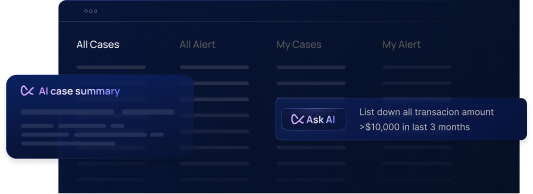
Case Management Systems
Once suspicious activity is detected, case management platforms organize investigations, track evidence, document decisions, and manage SAR filing workflows while maintaining comprehensive audit trails.
Practical tip: Integrate multiple tools into a unified compliance platform for maximum effectiveness.
What Is the Payment Investigation Process?
The payment investigation process follows a systematic methodology ensuring every suspicious transaction receives appropriate scrutiny while maintaining efficiency and regulatory compliance.
Step 1: Alert Review and Initial Detection
The process begins when monitoring tools flag a transaction or a manual review identifies concerning activity. Investigators review the alert to understand why the transaction was flagged and identify immediate red flags.
During this initial review, investigators determine whether the alert warrants full investigation or can be dismissed as a false positive. Some transactions might be flagged due to minor deviations from typical patterns but have clear, legitimate explanations readily available in customer files.
What to do: Examine the alert details, understand the rule or model that generated it, and assess whether obvious explanations exist before committing to full investigation.
Step 2: Preliminary Assessment
Conduct a quick assessment evaluating the alert's severity and determining investigation priority. Not every flagged transaction requires immediate, comprehensive investigation—some pose higher risk than others.
This assessment considers transaction size, customer risk rating, number of red flags present, and potential impact if the activity is indeed criminal. High-risk customers conducting large transactions to sanctioned jurisdictions receive immediate attention; low-risk customers with minor anomalies may receive standard review timelines.
What to do: Categorize alerts by priority (critical, high, medium, low) based on risk factors. Investigate critical alerts within hours; others can follow standard workflows.
Step 3: Information Gathering
Collect all relevant information about the transaction, including parties involved, transaction nature, amounts, dates, payment methods, and other pertinent details. Investigators compile customer account opening documentation, transaction history, communication records, and any previous investigation notes.
This step also includes gathering external information like adverse media searches, corporate registry lookups for business customers, and checking for connections to known financial crime networks.
What to do: Build a complete transaction timeline, identify all parties involved, collect supporting documentation, and search for similar past transactions.
Step 4: Contextual Analysis
Analyze the transaction in context by comparing it against the customer's profile, historical transaction patterns, stated business purpose, and known behaviors. Look for inconsistencies or anomalies that can't be explained by legitimate business evolution.
This analysis determines whether the transaction makes logical sense. Does a customer's occupation support their income sources? Do international transfers align with their business operations? Are spending patterns consistent with their lifestyle?
What to do: Create a customer behavior profile, map the transaction against expected patterns, identify specific inconsistencies, and document contextual factors that increase or decrease suspicion.
Step 5: Investigative Tools and Techniques
Utilize advanced investigative techniques including transaction pattern analysis to identify structuring or layering schemes, link analysis to uncover hidden relationships, geographic analysis to understand cross-border fund flows, and comparison against known typologies.
Investigators might also conduct open-source intelligence gathering, review social media for business verification, or consult with specialists for industry-specific transactions.
What to do: Apply multiple analytical techniques, cross-reference findings, and use visualization tools to identify patterns not obvious in raw data.
Step 6: Assessment and Decision Making
Based on comprehensive analysis, assess whether the transaction is genuinely suspicious and decide the appropriate course of action. If suspicious, determine whether to file a SAR, escalate to law enforcement, or implement enhanced monitoring.
This decision requires balancing available evidence, regulatory requirements, institutional risk tolerance, and potential impact on customer relationships. Decision-making should follow documented criteria to ensure consistency.
What to do: Evaluate all evidence objectively, apply institutional decision criteria, consult with compliance leadership on borderline cases, and document the decision rationale thoroughly.
Step 7: Documentation
Document every investigation step comprehensively. Documentation should include what triggered the alert, what information was gathered, what analysis was conducted, what was discovered, and why specific decisions were made.
This documentation may be reviewed by regulators, law enforcement, or internal auditors. It must demonstrate that the institution conducted thorough, good-faith investigation following established procedures.
What to do: Use standardized templates, include timestamps for all actions, attach supporting evidence, and write clearly enough that someone unfamiliar with the case can understand your investigation and decision.
Step 8: Feedback Loop and System Improvement
Provide feedback to improve monitoring systems based on investigation outcomes. If an investigation reveals new fraud patterns or indicators not captured by current rules, update system parameters to incorporate these insights.
This continuous improvement ensures monitoring systems evolve with emerging threats rather than remaining static.
What to do: Track investigation outcomes, identify patterns in false positives requiring rule tuning, document new typologies for system updates, and regularly review alert quality metrics.
How Do Banks Identify Suspicious Transactions?
Banks use multi-layered approaches combining technology, processes, and trained personnel to identify suspicious transactions throughout the customer lifecycle.
Banks deploy sophisticated transaction monitoring platforms analyzing every payment in real time transaction monitoring against customer risk profiles and hundreds of detection scenarios. These systems flag anomalies automatically, generating alerts for human review based on regulatory guidance, known fraud typologies, and institutional risk appetite.
Through comprehensive KYC programs, banks create detailed customer profiles during onboarding documenting expected transaction volumes, business activities, income sources, and geographic exposure. As transactions occur, banks compare actual activity against these documented expectations, triggering enhanced scrutiny when significant deviations appear.
Banks assign risk ratings to customers based on occupation, business type, geography, and other factors. High-risk customers face enhanced monitoring with lower alert thresholds and more frequent reviews, allocating investigative resources efficiently.
Banks also train front-line employees to recognize suspicious behavior during customer interactions, while continuously screening customers against sanctions lists, PEP databases, and adverse media.
Practical tip: Implement multiple detection layers—automated systems catch pattern-based anomalies; trained employees identify behavioral red flags; continuous screening catches external risk indicators.
What Is Suspicious Transaction Monitoring?
Suspicious transaction monitoring is the ongoing process of analyzing financial transactions to identify activity that may indicate money laundering, fraud, terrorist financing, or other financial crimes.
This monitoring operates continuously, examining every transaction as it occurs rather than relying on periodic reviews. Real-time monitoring enables immediate intervention when high-risk transactions are attempted.
Effective monitoring includes detection scenarios (pre-configured rules and machine learning models), customer risk profiling (dynamic assessments adjusting monitoring sensitivity), alert generation (automated flagging routed by severity), investigation workflows (structured processes ensuring consistency), and reporting mechanisms (enabling timely SAR filing).
Banks employ both transaction-based monitoring (analyzing individual payments) and behavior-based monitoring (identifying pattern changes over time). The most effective programs combine both approaches.
Practical tip: Review and tune monitoring scenarios quarterly. Track false positive rates, investigation outcomes, and missed detections to continuously improve effectiveness.
What Are the Legal and Compliance Requirements for Investigating Suspicious Transactions?
Investigating and reporting suspicious transactions involves navigating complex regulatory requirements that vary by jurisdiction but share common principles.
Laws and regulations differ by country, requiring institutions to understand jurisdiction-specific requirements for customer due diligence, record-keeping, and reporting suspicious activities. Most jurisdictions have stringent AML laws requiring compliance programs, customer due diligence, transaction monitoring, and suspicious activity reporting. Financial Action Task Force (FATF) standards provide baseline guidelines most countries incorporate into local regulations.
A key compliance requirement for brokerages and trusts alongside banks, is filing SARs with the relevant financial intelligence unit when transactions are suspected of relating to money laundering, terrorist financing, or other illicit activities. SARs must be filed within stipulated timeframes (often 30 days) while maintaining strict confidentiality to avoid "tipping off" subjects.
Financial institutions must develop comprehensive compliance programs including written policies, designated compliance officers, independent testing, and ongoing employee training. Programs must be risk-based with controls proportionate to institutional size and risk profile.
Regulations typically require retaining transaction records, customer documents, and investigation documentation for specified periods (often 5-7 years), readily accessible for regulatory examination.
Non-compliance can result in substantial fines (often millions or billions), criminal prosecution, loss of licenses, and devastating reputational damage.
Practical tip: Establish regular compliance training for all employees. Everyone plays a role in detecting and preventing financial crime.
What Should You Do If You Identify a Suspicious Transaction?
When you identify suspicious transaction indicators, follow a structured response protecting the institution while complying with regulatory obligations.
Document immediately what made the transaction suspicious, including specific red flags, dates, amounts, parties, and customer statements. Documentation should be factual and objective.
Report internally to your institution's MLRO, compliance department, or designated contact according to procedures. Don't delay—flag concerns immediately and let specialists investigate.
Never tip off customers about investigations or SAR filings. This is a criminal offense that can compromise law enforcement investigations. Continue providing normal service.
Preserve all evidence including documentation, communications, and transaction records. Don't alter or destroy materials related to suspicious activity.
Follow institutional procedures to ensure consistent, compliant responses.
Practical tip: When in doubt, report. Regulators prefer overly cautious internal reports over unreported suspicious activity.
Practical Tips for Investigating Suspicious Transactions
Establish Clear Protocols - Develop standardized investigation procedures specifying information to gather, analysis to conduct, documentation requirements, and decision criteria.
Use Investigation Checklists - Create checklists for different transaction types ensuring investigators don't overlook critical review steps.
Prioritize Risk-Based Investigation - Allocate resources based on risk—high-risk customers conducting large transactions receive comprehensive investigation; low-risk anomalies receive proportionate review.
Leverage Technology - Use link analysis, visualization tools, and automated data gathering to enhance investigation efficiency without replacing human judgment.
Maintain Time Standards - Establish timeframes for completing investigations based on alert priority.
Build Subject Matter Expertise - Develop institutional expertise in common customer segments for more effective investigation.
Create Feedback Mechanisms - Track investigation outcomes and use data to improve detection systems.
Document Clearly - Write conclusions clearly enough that regulators unfamiliar with the case can understand your reasoning.
Train Continuously - Provide regular training on emerging typologies, new regulations, and investigation techniques.
Foster Collaboration - Encourage communication between compliance, fraud teams, customer-facing staff, and IT.
Frequently Asked Questions
What makes a transaction suspicious in banking?
A transaction becomes suspicious when it deviates from expected customer behavior patterns, lacks clear legitimate purpose, involves unusual complexity, connects to high-risk jurisdictions, or exhibits characteristics matching known money laundering or fraud typologies. Context matters—a transaction that is suspicious in one scenario may be perfectly normal in another.
How do banks detect suspicious activity on accounts?
Banks use automated transaction monitoring systems analyzing every transaction against customer risk profiles and detection rules, behavioral analytics identifying pattern deviations, continuous watchlist screening, employee observations of unusual customer behavior, and data analysis revealing connections between suspicious accounts or entities. Multiple detection methods create comprehensive coverage.
What is the bank fraud investigation process?
Bank fraud investigations involve: (1) detecting suspicious activity through monitoring or reports, (2) gathering transaction details and customer information, (3) analyzing patterns and connections, (4) determining if fraud occurred and its extent, (5) documenting findings thoroughly, (6) deciding whether to file SARs or refer to law enforcement, and (7) implementing controls preventing similar fraud. Investigations must balance speed with thoroughness.
What tools notify you of potential risks in financial behavior?
Transaction monitoring platforms, behavioral analytics systems, real-time payment screening tools, link analysis software, watchlist screening solutions, case management platforms, fraud detection systems using machine learning, and automated alert routing systems all provide risk notifications. Integration between tools creates comprehensive risk coverage and efficient investigation workflows.
How long does a suspicious transaction investigation take?
Investigation duration varies by complexity. Simple cases with clear explanations might resolve in hours; complex cases involving multiple accounts, entities, or jurisdictions could take weeks. Regulatory timeframes often require SAR filing within 30 days of initial detection. Institutions should establish investigation timeframes based on alert priority and complexity.
Who determines if a transaction is suspicious?
Trained compliance investigators, AML analysts, and Money Laundering Reporting Officers (MLROs) determine if transactions are suspicious after conducting thorough investigation. While automated systems flag potential suspicious activity, human experts make final determinations based on context, evidence, and regulatory guidance. Decision-making should follow documented institutional criteria.
What happens after a suspicious activity report is filed?
After SAR filing, the financial intelligence unit (FIU) receives the report and may share it with law enforcement for investigation. The filing institution continues monitoring the customer for additional suspicious activity and may implement enhanced due diligence. Institutions maintain SAR confidentiality and cannot inform customers about filings. Law enforcement may or may not contact the institution for additional information.
Can you tell a customer their transaction was flagged as suspicious?
No. Financial institutions must not inform customers that transactions have been flagged as suspicious or that SARs have been filed about their activity. "Tipping off" is a criminal offense that can compromise law enforcement investigations and expose the institution to legal liability. Continue normal customer service without indicating any investigation is occurring.
What are common examples of suspicious activity in banking?
Common examples include: structuring deposits to avoid reporting requirements, rapid movement of funds through multiple accounts, transactions inconsistent with stated business purpose, payments to/from high-risk jurisdictions without clear reason, use of shell companies or nominees, cash transactions significantly above customer norms, transactions right after account opening, and activity matching known money laundering typologies.
How do you report suspected money laundering?
Report suspected money laundering internally to your institution's MLRO or compliance department immediately. They will conduct an investigation and determine if SAR filing is required. External reporting (to FIUs or law enforcement) should only be done through official institutional channels by authorized personnel. Never attempt to investigate or report money laundering independently without involving compliance.
Key Takeaways
Suspicious doesn't mean criminal - Unusual transactions require investigation, not proof of wrongdoing
Context is critical - Same transaction might be normal for one customer but suspicious for another
Use multiple detection methods - Combine automated monitoring, analytics, screening, and human observation
Document thoroughly - Comprehensive documentation protects institutions and demonstrates compliance
Never tip off customers - Informing customers about investigations is a criminal offense
Follow investigation standards - Use standardized procedures and timeframes
Continuously improve - Use outcomes to tune monitoring and reduce false positives
Prioritize by risk - Allocate resources according to transaction and customer risk levels
Conclusion
Investigating suspicious transactions is a critical defense against money laundering, fraud, and terrorist financing, supported by AI forensics. The process combines sophisticated monitoring technology with human expertise to identify financial crime while minimizing false positives.
Effective programs follow structured methodologies ensuring every suspicious transaction receives appropriate scrutiny with comprehensive documentation demonstrating compliance efforts. They balance speed with thoroughness, meeting regulatory timelines while conducting rigorous analysis.
Non-compliance exposes institutions to massive fines, criminal prosecution, license revocation, and reputational destruction. Non-compliance with AML requirements goes beyond avoiding penalties. Robust programs protect financial system integrity, deny criminals banking access, and help law enforcement disrupt criminal networks.
Success requires continuous improvement. Investigation procedures must evolve with emerging threats. Monitoring systems need regular tuning. Staff require ongoing training on new typologies and regulatory changes.
By investing in robust investigation capabilities—advanced monitoring tools, skilled investigators, clear procedures, comprehensive training, and continuous improvement—financial institutions protect themselves while contributing to the global fight against financial crime.




.svg)






.webp)