AT A GLANCE
Risk-based transaction monitoring is a targeted approach that analyzes financial transactions to detect fraud, money laundering, and other illicit activities by focusing resources on high-risk customers and transactions rather than treating all activity equally. With financial crime losses exceeding $3.1 trillion globally in 2023 and regulatory penalties reaching record levels, effective transaction monitoring is no longer optional—it's essential for survival. This comprehensive guide explains what risk-based transaction monitoring is, how to implement it, how to set up effective alerting systems, and what financial institutions need to know to stay compliant while minimizing false positives.
What Is Risk-Based Transaction Monitoring?
Risk-based transaction monitoring is a systematic process that analyzes customer transactions to identify patterns indicating financial crime. Unlike traditional monitoring that treats all transactions equally, risk-based approach allocates resources proportionate to actual threats by assessing each customer's risk level and monitoring their activity accordingly.
This methodology originated from regulatory guidance—particularly from the Financial Action Task Force (FATF) and the Bank Secrecy Act—that explicitly requires financial institutions to adopt risk-based approaches. The logic is straightforward: a politically exposed person conducting cross-border wire transfers to high-risk jurisdictions requires more scrutiny than a domestic retail customer making routine debit card purchases.
Core Components of Transaction Monitoring Systems
Effective transaction monitoring systems consist of four essential elements that work together:
- Customer risk assessment: Evaluating each customer's inherent risk based on factors like industry, geography, transaction volumes, and whether they are politically exposed persons (PEPs).
- Continuous transaction monitoring: Analyzing transactions in real-time or near-real-time against predefined rules and behavioral patterns to detect anomalies.
- Alert investigation: Reviewing flagged transactions to determine whether they represent genuine threats or false positives, with clear escalation procedures.
- Regulatory reporting: Filing Suspicious Activity Reports (SARs) and other required documentation when warranted, maintaining detailed audit trails.
Why Is Risk-Based Transaction Monitoring Critical for Financial Institutions?
Transaction monitoring is essential because it's the primary mechanism financial institutions use to detect money laundering, terrorist financing, fraud, and other financial crimes in real-time. Without effective monitoring, institutions face severe regulatory penalties, operational losses, and reputational damage.
Regulatory Compliance Requirements
Multiple regulations mandate transaction monitoring:
- Bank Secrecy Act (BSA): Requires U.S. financial institutions to maintain programs that detect and report suspicious activities, with civil penalties up to $100,000 per violation and criminal penalties including imprisonment.
- EU Anti-Money Laundering Directives: Mandate enhanced due diligence and continuous monitoring of high-risk customers across all EU member states, with penalties reaching 10% of annual turnover.
- FATF Recommendations: Provide international standards requiring financial institutions to implement risk-based transaction monitoring as part of comprehensive AML programs.
Non-compliance with AML regulations can result in significant financial penalties. In 2023 alone, global financial institutions paid over $5.4 billion in AML-related fines, with transaction monitoring deficiencies cited as a primary cause in many enforcement actions.
Financial Crime Prevention
Beyond compliance, effective transaction monitoring protects institutions from direct financial losses. Money laundering, fraud, and other financial crimes cost the global economy an estimated $3.1 trillion annually. Transaction monitoring serves as the frontline defense, detecting suspicious activity before it results in significant losses.
For fintechs and digital banks, transaction monitoring is particularly critical. Their digital-first business models and rapid customer acquisition create vulnerabilities that criminals actively exploit. Strong monitoring systems demonstrate to partner banks, payment processors, and regulators that the institution can manage these risks effectively.
What Is the Difference Between Real-Time and Batch Transaction Monitoring?
Transaction monitoring systems operate on two primary models: batch processing and real-time monitoring. The choice between them significantly impacts detection capabilities, operational costs, and the ability to prevent fraud before it completes.
Batch-Based Transaction Monitoring
Traditional batch monitoring collects transactions over a period (typically daily or weekly) and analyzes them together in scheduled processing runs. This approach offers several advantages:
- Lower computational costs since processing occurs during off-peak hours
- Easier pattern detection across multiple transactions over time
- Simpler system architecture and maintenance
- Better suited for analyzing historical patterns and trends
However, batch monitoring has a critical limitation: by the time suspicious transactions are detected, funds may have already been transferred and withdrawn. For instant payment systems, cryptocurrency transactions, or wire transfers, this delay can make recovery impossible.
Real-Time Transaction Monitoring
Real-time monitoring evaluates transactions at the point of initiation, enabling institutions to block or delay suspicious transfers immediately. This approach requires:
- High-performance computing infrastructure to process transactions within milliseconds
- Streamlined rules that can execute quickly without causing transaction delays
- Integration with payment processing systems to enable transaction holds
- Clear procedures for resolving holds and communicating with customers
Real-time monitoring is particularly important for:
- Instant payment systems (P2P transfers, mobile payments)
- Cryptocurrency transactions that settle irreversibly
- International wire transfers where recovery is difficult
- High-value transactions where potential losses are significant
Hybrid Approaches
Most modern institutions use hybrid models that combine watchlist screening for high-risk scenarios with batch processing for comprehensive pattern analysis. This approach balances detection effectiveness with operational efficiency.
How Do You Implement Risk-Based Transaction Monitoring?
Implementing effective transaction monitoring requires systematic planning and execution across seven key phases. Each phase builds on the previous one to create a comprehensive monitoring program.
Step 1: Conduct Comprehensive Risk Assessment
Begin by identifying and evaluating your institution's specific money laundering and fraud risks. This assessment should analyze:
- Customer demographics and risk profiles
- Products and services offered (particularly high-risk ones like wire transfers, cryptocurrency, or correspondent banking)
- Geographic exposure to high-risk jurisdictions
- Distribution channels and how customers access services
- Transaction volumes, values, and typical patterns
- Historical suspicious activity and fraud losses
Document findings in a formal risk assessment report that prioritizes risks by likelihood and potential impact. This document becomes the foundation for all subsequent monitoring decisions.
Step 2: Select Appropriate Monitoring Technology
Choose a transaction monitoring system that aligns with your institution's size, complexity, and risk profile. Key selection criteria include:
- Real-time vs. batch processing capabilities
- Scalability to handle current and projected transaction volumes
- Integration capabilities with existing core banking and payment systems
- Rules engine flexibility and ease of configuration
- Machine learning and AI capabilities for advanced detection
- Case management workflow tools
- Reporting and audit trail functionality
- Vendor support and system update frequency
Step 3: Configure Monitoring Rules and Scenarios
Develop monitoring rules directly tied to your risk assessment findings. Each rule should target specific money laundering or fraud typologies identified as relevant to your institution. Common scenarios include:
- Structuring: Multiple transactions just below reporting thresholds
- Rapid movement of funds: Money entering and exiting accounts quickly
- High-risk geography: Transactions involving sanctioned or high-risk countries
- Unusual patterns: Activity inconsistent with customer profiles
- Round-dollar amounts: Suspicious transaction values
- Velocity checks: Sudden spikes in transaction frequency or volume
Rules should be dynamic with adjustable thresholds based on customer risk levels. High-risk customers warrant lower thresholds and more sensitive monitoring than low-risk customers.
Step 4: Integrate Data Sources
Connect the monitoring system to all relevant internal and external data sources:
- Internal sources: Core banking systems, payment processors, customer relationship management (CRM) databases, KYC/due diligence records
- External sources: Sanction lists (OFAC, UN, EU), politically exposed persons (PEP) databases, adverse media screening, law enforcement databases
Data quality is critical—inaccurate or incomplete data leads to false positives and missed detections. Establish data validation processes and regular quality audits.
Step 5: Test Through Simulation and Back-Testing
Before going live, validate system effectiveness through:
- Back-testing: Run rules against historical transaction data to assess detection rates and false positive volumes
- Scenario testing: Create test cases representing known money laundering typologies to verify the system detects them
- Tuning: Adjust thresholds and parameters based on test results to optimize performance
Testing typically requires 3-6 months to properly tune rules to your specific transaction patterns and customer base.
Step 6: Train Compliance Teams
Ensure all relevant personnel understand the monitoring system, investigation procedures, and escalation protocols. Training should cover:
- System operation and alert review workflows
- Money laundering and fraud typologies
- Investigation techniques and documentation requirements
- SAR filing procedures and timing requirements
- Regulatory expectations and recent enforcement trends
Step 7: Establish Continuous Improvement Process
Transaction monitoring is not a set-and-forget system. Implement ongoing review processes including:
- Monthly alert quality reviews
- Quarterly rule effectiveness assessments
- Regular model validation (annually or when significant changes occur)
- Monitoring of key performance indicators (alert-to-SAR ratios, false positive rates, investigation timeframes)
- Updates for new typologies and regulatory guidance
How Do You Set Up Rules to Flag High-Risk Transactions?
Setting up effective transaction monitoring rules requires balancing detection sensitivity with operational efficiency. Rules that are too strict generate excessive false positives, while overly lenient rules miss genuine threats.
Rule Design Principles
Effective rules follow several core principles:
- Risk-based thresholds: Set different trigger points based on customer risk levels. A $5,000 cash deposit might be routine for a high-volume business but suspicious for a dormant personal account.
- Multiple indicators: Combine several factors rather than relying on single triggers. For example, flag transactions that are both high-value AND involve high-risk jurisdictions AND occur outside normal business hours.
- Time-based logic: Consider velocity and timing. Detect patterns like multiple transactions in rapid succession or unusual activity outside the customer's normal schedule.
- Peer comparison: Compare customer behavior against similar customers. A transaction volume normal for one customer type may be anomalous for another.
Common High-Risk Transaction Scenarios
Build rules targeting these priority scenarios:
1. Structuring Detection
Flag multiple transactions just below regulatory reporting thresholds (e.g., multiple $9,000 deposits when $10,000 triggers reporting). Look for patterns across accounts, timeframes, and locations.
2. Rapid Movement of Funds
Detect accounts where funds are deposited and immediately withdrawn or transferred, particularly when there's no apparent business purpose for the intermediate account.
3. Geographic Risk
Monitor transactions involving sanctioned countries or jurisdictions with weak AML controls. Cross-reference with FATF high-risk country lists and sanctions databases.
4. Profile Deviation
Alert when customer activity deviates significantly from their established baseline. This includes sudden volume increases, changes in counterparty types, or new transaction patterns.
Rule Tuning and Optimization
Initial rule configurations almost always require adjustment. Establish a systematic tuning process:
- Track alert disposition rates (percentage of alerts that result in SARs vs. those closed as false positives)
- Analyze false positive patterns to identify unnecessary triggers
- Conduct lookback testing when adjusting rules to ensure legitimate suspicious activity isn't missed
- Document all threshold changes and the rationale behind them
Target alert-to-SAR ratios between 5-15% as a general guideline. Ratios below 5% may indicate overly sensitive rules, while ratios above 15% might suggest rules are too lenient.
How Do You Build a Risk Alerting System for Banking Users?
A risk alerting system is the operational infrastructure that detects suspicious transactions, prioritizes them for investigation, and manages the alert lifecycle from creation through resolution. Building an effective system requires careful attention to workflow design, technology integration, and user experience.
Alert Generation and Prioritization
Design your alerting system to categorize and prioritize alerts based on risk severity:
- Critical alerts: Require immediate investigation (sanctions matches, politically exposed persons, transactions to high-risk jurisdictions)
- High priority: Investigate within 24 hours (unusual high-value transactions, rapid fund movement, multiple simultaneous alerts)
- Medium priority: Review within 3-5 business days (moderate pattern deviations, lower-value anomalies)
- Low priority: Queue for periodic review (minor threshold triggers, routine pattern variations)
Implement automated scoring that assigns priority levels based on multiple risk factors. This ensures analysts focus on the highest-risk alerts first.
Investigation Workflow Design
Create standardized investigation workflows that guide analysts through consistent review processes:
- Initial review: Analyst examines the alert details, customer profile, and transaction history
- Context gathering: Collect additional information through customer outreach, internal records, and external data sources
- Analysis: Determine whether activity has legitimate business purpose or indicates potential financial crime
- Decision: Close as false positive, escalate for enhanced due diligence, file SAR, or exit customer relationship
- Documentation: Record investigation findings, decisions, and supporting evidence
Case Management Integration
Your alerting system should integrate with case management tools that:
- Aggregate related alerts into single cases to prevent duplicate investigations
- Provide complete customer histories and previous investigation results
- Track investigation status and aging
- Generate audit trails for regulatory examinations
- Support SAR filing workflows with pre-populated templates
Performance Monitoring and Reporting
Build dashboards that track key alerting system metrics:
- Alert volumes by type and priority
- Average investigation time by alert category
- Alert disposition outcomes (SAR filed, false positive, enhanced monitoring)
- False positive rates by scenario
- Aging of open alerts and cases
- Analyst productivity and workload distribution
What Are the Key Benefits of Risk-Based Transaction Monitoring?
Risk-based transaction monitoring delivers significant operational and strategic advantages compared to traditional one-size-fits-all approaches.
Improved Detection Rates
By focusing monitoring intensity on high-risk areas, institutions significantly improve their ability to identify genuine financial crimes. Resources concentrate where threats are highest rather than being spread thin across all activity. Studies show properly implemented risk-based monitoring can improve detection rates by 40-60% compared to flat-threshold approaches.
Reduced False Positives
False positives—alerts that turn out to be legitimate activity—consume the majority of compliance resources at most institutions. Traditional monitoring systems can generate false positive rates exceeding 95%, meaning analysts spend most of their time investigating benign transactions.
Risk-based approaches reduce false positives by:
- Setting appropriate thresholds for different customer segments
- Incorporating contextual information about expected customer behavior
- Using machine learning to identify truly anomalous patterns
- Applying lighter monitoring to demonstrably low-risk customers
Institutions implementing risk-based monitoring typically see false positive reductions of 30-50%, freeing analysts to focus on genuine threats.
Better Resource Allocation
Risk-based monitoring allows institutions to deploy limited compliance resources where they'll have the greatest impact. Rather than spreading analysts across thousands of low-value alerts, teams can concentrate on high-risk scenarios that pose the greatest threat.
This efficiency translates to cost savings. Institutions report 20-40% reductions in compliance costs after transitioning from traditional to risk-based monitoring, despite often detecting more genuine suspicious activity.
Scalability and Adaptability
Risk-based systems scale more effectively as transaction volumes grow. By adjusting rules and thresholds based on risk profiles rather than absolute values, monitoring remains effective even as the institution expands.
These systems also adapt more readily to evolving threats. When new money laundering typologies emerge, institutions can update rules for high-risk segments while leaving low-risk monitoring unchanged. This targeted approach minimizes disruption and implementation time.
Enhanced Customer Experience
Risk-based monitoring improves customer experience by reducing unnecessary friction for legitimate customers. Low-risk customers face fewer transaction delays and verification requests, while enhanced monitoring focuses on truly suspicious activity. This balance between security and convenience is particularly important for fintechs competing on user experience.
What Are the Biggest Challenges in Implementing Transaction Monitoring Systems?
While risk-based transaction monitoring offers significant benefits, implementation presents several challenges that institutions must address systematically.
Data Quality and Integration
Poor data quality is the leading cause of monitoring system failures. Transaction monitoring requires accurate, complete, and timely data from multiple sources. Common data issues include:
- Incomplete customer profiles lacking critical risk indicators
- Inconsistent data formats across different systems
- Missing or delayed transaction details
- Duplicate records and data integrity problems
- Outdated customer information
Address data quality issues before implementing monitoring systems. Establish data governance processes, implement validation rules, and conduct regular audits to maintain data integrity.
System Complexity and Integration
Transaction monitoring systems must integrate with multiple existing platforms including core banking systems, payment processors, customer databases, and compliance tools. These integrations are technically complex and prone to errors.
Legacy system limitations can constrain monitoring capabilities. Older core banking platforms may not provide real-time data feeds or may lack API capabilities for seamless integration. Institutions often require middleware or data warehousing solutions to bridge these gaps.
Alert Fatigue and Resource Constraints
Even with optimized rules, transaction monitoring generates significant alert volumes. Analysts can become desensitized to alerts when overwhelmed with high volumes, particularly when most prove to be false positives.
Many institutions struggle with compliance staffing. Finding and retaining qualified analysts with AML expertise is challenging, particularly for smaller institutions and fintechs. This staffing constraint makes alert management even more critical.
Keeping Pace with Evolving Threats
Money launderers continuously adapt their techniques to evade detection. Transaction monitoring systems must evolve to address new typologies including:
- Cryptocurrency-related money laundering
- Trade-based money laundering schemes
- Transaction laundering through payment processors
- Synthetic identity fraud
- Real-time payment exploitation
Institutions need processes for monitoring emerging threats and updating detection rules accordingly. This requires ongoing threat intelligence, industry collaboration, and system flexibility.
Balancing Security with Customer Experience
Effective monitoring can create friction in the customer experience. Transaction delays while alerts are reviewed, requests for additional documentation, and account restrictions can frustrate legitimate customers and drive them to competitors.
For fintechs in particular, this tension between security and user experience is acute. Digital-first customers expect instant transactions and seamless experiences. Finding the right balance requires sophisticated monitoring that minimizes false positives while maintaining strong detection capabilities.
How Does Transaction Monitoring Help Prevent Money Laundering?
Transaction monitoring is the frontline defense against money laundering, enabling financial institutions to detect and disrupt criminal activity before it succeeds. Understanding how monitoring prevents money laundering demonstrates why robust systems are essential.
Detecting the Three Stages of Money Laundering
Money laundering typically occurs in three stages, and transaction monitoring can detect activity at each phase:
1. Placement
Criminals introduce illicit funds into the financial system. Monitoring detects placement through alerts for large cash deposits, structuring patterns, and transactions inconsistent with customer profiles.
2. Layering
Money moves through multiple transactions to obscure its origin. Systems identify layering by flagging rapid fund movement, complex transaction chains, and transactions lacking clear business purpose.
3. Integration
Laundered funds return to the legitimate economy. Monitoring catches integration through detection of transactions with shell companies, unusual real estate purchases, or investments inconsistent with stated income sources.
Real-Time Intervention
Real-time monitoring enables institutions to stop money laundering attempts before they complete. When suspicious transactions are detected during processing, institutions can:
- Place holds on transactions for manual review
- Request additional documentation before allowing the transaction
- Block transactions entirely if they violate sanctions or pose unacceptable risks
- Notify law enforcement of potential criminal activity
This intervention capability is particularly important for irreversible transactions like cryptocurrency transfers or instant payments where funds cannot be recovered once the transaction completes.
Supporting Law Enforcement Investigations
Transaction monitoring generates the Suspicious Activity Reports (SARs) that form the foundation of financial crime investigations. These reports provide law enforcement with:
- Detailed transaction records and patterns
- Connections between accounts and individuals
- Evidence of money movement and hiding techniques
- Timeline reconstruction of criminal financial activity
In 2023, U.S. financial institutions filed over 3.6 million SARs, directly contributing to thousands of criminal investigations, prosecutions, and asset forfeitures.
Deterrence Effect
Effective monitoring creates a deterrent effect. When criminals know institutions have sophisticated detection capabilities, they avoid those institutions or seek alternative laundering methods. This protective effect extends beyond individual institutions—strong monitoring across the financial sector makes money laundering more difficult and expensive overall.
Frequently Asked Questions About Transaction Monitoring
What is transaction monitoring in AML compliance?
Transaction monitoring is the continuous analysis of customer financial transactions to detect patterns indicating money laundering, fraud, or other financial crimes. It uses automated systems with predefined rules and machine learning algorithms to flag suspicious activity for investigation. Effective monitoring is a regulatory requirement under AML laws including the Bank Secrecy Act and FATF recommendations.
How often should transaction monitoring rules be updated?
Rules should be reviewed quarterly at minimum, with formal validation annually or when significant changes occur (new products, market expansion, regulatory updates, or emerging typologies). However, threshold tuning may be needed more frequently—many institutions adjust thresholds monthly based on alert quality metrics. Document all changes with clear rationale and conduct lookback testing to ensure modifications don't create blind spots.
What is a good false positive rate for transaction monitoring?
While there's no universal standard, well-tuned systems typically achieve false positive rates between 80-95%. This means 5-20% of alerts result in escalation, enhanced monitoring, or SAR filing. Rates below 80% may indicate overly lenient rules that miss genuine threats, while rates above 95% suggest rules are too sensitive, wasting resources on benign activity. Focus on optimizing the alert-to-SAR conversion rate (typically 5-15%) as a more meaningful metric.
Can small financial institutions use risk-based transaction monitoring?
Yes, and they should. Risk-based monitoring is actually more critical for smaller institutions with limited compliance resources. The key is right-sizing the approach—smaller institutions don't need enterprise-scale systems. Many vendors offer cloud-based solutions designed for community banks and credit unions with reasonable pricing and simpler implementation. The risk-based methodology (focusing on high-risk areas) is equally applicable regardless of institution size.
How does machine learning improve transaction monitoring?
Machine learning enhances monitoring by identifying complex patterns that rules-based systems miss, reducing false positives through behavioral analysis, adapting to changing customer behavior automatically, and detecting previously unknown money laundering typologies. ML models learn what normal looks like for each customer and flag deviations more accurately than static rules. However, ML should augment, not replace, rules-based monitoring—the combination delivers optimal results.
What happens when a transaction is flagged as suspicious?
Flagged transactions enter an investigation workflow where analysts review the alert, examine customer history and supporting information, determine if activity has legitimate business purpose, and decide on appropriate action (close as false positive, request additional information, enhance monitoring, file SAR, or exit customer relationship). For critical alerts, transactions may be held pending review. All investigations must be documented with clear rationale for regulatory compliance.
How long does it take to implement a transaction monitoring system?
Implementation timelines vary significantly based on institution size and system complexity. Small to mid-size institutions can implement basic systems in 3-6 months. Larger institutions or those with complex requirements typically need 9-18 months. Critical phases include system selection (1-3 months), data integration (2-6 months), rule configuration and testing (3-6 months), and user training and optimization (ongoing). Plan for 3-6 additional months of tuning after go-live.
What are the key performance indicators for transaction monitoring?
Essential KPIs include: alert volume trends (tracking increases/decreases by scenario), alert-to-SAR conversion rate (percentage of alerts resulting in SARs), false positive rate by scenario, average investigation time, aged alert percentages (alerts open beyond target timeframes), SAR filing timeliness, scenario coverage (percentage of identified risks with monitoring rules), and system availability/performance metrics. Track these monthly and report to senior management quarterly.
How do fintechs implement transaction monitoring with limited resources?
Fintechs should prioritize cloud-based monitoring solutions that don't require extensive IT infrastructure, start with core scenarios covering the highest-risk typologies rather than comprehensive coverage from day one, leverage API-based platforms that integrate quickly with existing systems, consider managed services or outsourced alert investigation to supplement limited staff, and implement phased rollouts that align with business growth and regulatory requirements.
What regulatory penalties apply for transaction monitoring failures?
Penalties vary by jurisdiction and severity but can include: civil monetary penalties from regulators (often millions to billions of dollars), consent orders requiring extensive remediation programs, restrictions on business activities or growth, increased regulatory oversight and examination frequency, criminal charges against institutions and individual executives, and reputational damage that impacts customer and investor confidence. In 2023, global AML penalties exceeded $5.4 billion, with monitoring deficiencies frequently cited.
Practical Tips for Effective Transaction Monitoring
Start Simple, Then Expand
Don't try to monitor everything at once. Begin with 5-7 core scenarios covering your highest-risk typologies (structuring, rapid movement, geographic risk, profile deviation). Ensure these work effectively before adding additional scenarios. This phased approach prevents overwhelming your team and allows proper tuning of each rule set.
Treat Data Quality as Priority One
Transaction monitoring is only as good as the data feeding it. Before implementation, audit your customer data, transaction records, and risk ratings for completeness and accuracy. Establish data validation rules that prevent incomplete records from entering the system. Poor data quality is the number one cause of monitoring failures—fix it first.
Plan for Continuous Tuning
Out-of-the-box rules never work perfectly. Budget 3-6 months post-implementation for intensive tuning. Track alert quality metrics weekly, analyze false positive patterns monthly, and adjust thresholds based on data. Establish a formal tuning committee with representatives from compliance, operations, and IT that meets monthly to review performance and approve changes.
Document Everything
Maintain detailed documentation of your monitoring approach, rule configurations, tuning decisions, and investigation procedures. Regulators will ask why you chose specific thresholds, how you validated effectiveness, and what changes you've made over time. Strong documentation demonstrates thoughtful risk management and can significantly reduce regulatory scrutiny and penalties.
Invest in Analyst Training
The best monitoring system fails without skilled analysts. Provide comprehensive training on money laundering typologies, investigation techniques, and your specific system capabilities. Conduct regular refresher training and case study reviews. Consider external certifications (CAMS, CFCS) for senior analysts. Remember: technology flags suspicious activity, but human judgment determines outcomes.
Leverage Industry Intelligence
Don't operate in isolation. Join industry groups like ACAMS, attend AML conferences, and participate in information-sharing networks. FinCEN advisories, FATF typology reports, and industry working groups provide valuable intelligence on emerging threats that should inform your monitoring approach. Criminals share tactics—institutions should share defenses.
Balance Automation with Human Judgment
Automate what you can—data collection, initial screening, alert generation, basic triage—but preserve human oversight for critical decisions. Machine learning can improve efficiency dramatically, but don't fully automate SAR filing decisions or customer relationship exits. These require contextual judgment that only experienced analysts can provide. The goal is augmented intelligence, not artificial replacement.
The Future of Transaction Monitoring
Transaction monitoring continues to evolve as financial crime becomes more sophisticated and technology advances. The future will see increased adoption of artificial intelligence and machine learning for pattern detection, real-time monitoring becoming the standard rather than the exception, greater collaboration between institutions through information-sharing networks, and integration of blockchain analytics for cryptocurrency monitoring.
Regulatory expectations will continue to rise. Institutions that view transaction monitoring as merely a compliance checkbox will struggle, while those that embrace it as a strategic capability will thrive. The difference lies in treating monitoring not as a cost center but as an investment in operational resilience, customer trust, and sustainable growth.
For financial institutions and fintechs, the imperative is clear: implement robust, risk-based transaction monitoring, and a modern AML compliance solution that detects financial crime effectively while operating efficiently. This requires the right technology, skilled personnel, quality data, and continuous improvement. Institutions that get this right protect themselves from regulatory penalties, reduce fraud losses, and build the foundation for long-term success.
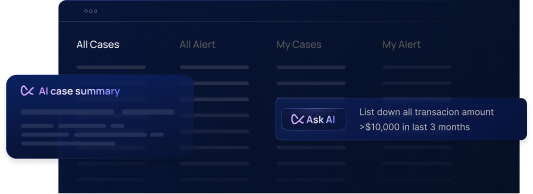
Transform Your Transaction Monitoring with Flagright
Flagright's cutting-edge transaction monitoring platform offers real-time analysis, advanced AI-powered detection, dynamic risk scoring, and seamless integration with your existing systems. Built specifically for fintechs, digital banks, and neobanks, our solution combines sophisticated monitoring capabilities with an intuitive user experience, while AI forensics helps teams investigate alerts faster and build stronger cases.
With implementation timelines as fast as 4 days, Flagright empowers your compliance teams to stay ahead of evolving risks while minimizing false positives and operational costs. Our platform adapts to your institution's unique risk profile, scales with your growth, and keeps pace with changing regulatory requirements.
Request a demo today to see how Flagright can enhance your transaction monitoring capabilities and achieve your AML compliance goals.




.svg)






.webp)