AT A GLANCE
Invoice fraud costs businesses billions annually through fake invoices, duplicate billing, and payment redirection schemes. Thanks to the integration of digital tools and platforms, anyone can create invoices in seconds. This guide reveals how to detect fraudulent invoices, implement prevention strategies, and protect your business from the most common invoice scams targeting companies today.
What Is Invoice Fraud and Why Is It Increasing?
Invoice fraud occurs when fraudsters present false or altered invoices to extract unauthorized payments or remittances from businesses. The digitization of business operations has created unprecedented opportunities for criminals to exploit payment systems.
Recent data shows invoice fraud incidents have surged 73% over the past five years. The shift to remote work, automated payment approvals, and electronic invoicing has expanded the attack surface for fraudsters. Where traditional paper-based systems required physical document forgery, today's criminals can create convincing fake invoices using readily available templates and intercept email communications to redirect legitimate payments.
The financial impact extends beyond direct monetary loss. Companies face regulatory penalties, damaged vendor relationships, operational disruptions, and reputational harm that can take years to repair. Small and medium-sized businesses are particularly vulnerable, often lacking the sophisticated fraud detection systems that larger enterprises deploy.
Key Driver: The average employee processes 500+ invoices monthly, creating cognitive overload that fraudsters exploit. High transaction volumes combined with tight payment deadlines create perfect conditions for invoice fraud to slip through undetected.
How Do Fraudsters Commit Invoice Fraud?
Understanding fraud techniques is essential for building effective defenses. Here are the seven most common invoice fraud schemes:
1. Fake Invoice Fraud
Criminals send invoices for products or services never ordered or delivered. These fake invoices often mimic legitimate vendors, using similar company names, logos, and formatting to appear authentic. The fraudster hopes the invoice will be paid without proper verification.
2. Duplicate Invoice Schemes
The same legitimate invoice is submitted multiple times, banking on administrative oversight. In high-volume accounts payable departments, duplicate invoices can easily slip through if proper controls aren't in place. Fraudsters may slightly alter invoice numbers or dates to avoid detection.
3. Overbilling and Inflated Invoices
A genuine vendor relationship exists, but the invoice amount exceeds the agreed price. This can involve inflated quantities, unauthorized price increases, or charges for services not rendered. Overbilling is particularly effective because the vendor appears legitimate, reducing scrutiny.
4. Phantom Supplier Fraud
Fraudsters create entirely fictitious vendors in a company's payment system. This often involves internal collusion, where an employee sets up fake vendor accounts and approves payments to themselves or accomplices. Phantom suppliers appear in accounting systems with complete documentation but no actual business operations.
5. Invoice Manipulation and Altered Invoices
Legitimate invoices are intercepted and modified before payment. Criminals change bank account details, payment amounts, or recipient information. This frequently occurs through business email compromise, where fraudsters gain access to email communications between companies and their suppliers.
6. Payment Redirection Fraud
Also called invoice redirect fraud, this sophisticated scheme involves impersonating a legitimate vendor to request payment details be changed. The fraudster may claim a bank account change, new payment portal, or updated wire transfer instructions. By the time the real vendor follows up on non-payment, the money is long gone.
7. Business Email Compromise (BEC)
Cybercriminals hack or spoof business email accounts to manipulate invoice payments. They may impersonate executives requesting urgent payments, vendors notifying of account changes, or accounting staff seeking payment approvals. BEC attacks have cost businesses over $43 billion globally since 2016.
What Are the Red Flags of Fraudulent Invoices?
Detecting invoice fraud requires vigilance and systematic verification. Watch for these warning signs:
Vendor Red Flags:
- New vendors with urgent payment requests
- Vendors with PO Box addresses or no physical location
- Similar names to established suppliers (typosquatting)
- Unusual or offshore bank account details
- Resistance to standard verification procedures
Invoice Red Flags:
- Missing or incorrect purchase order numbers
- Round numbers or estimates rather than precise amounts
- Invoice numbers that don't follow logical sequences
- Dates that don't align with service delivery
- Poor quality formatting or grammatical errors
Payment Red Flags:
- Sudden changes to established payment details
- Requests to bypass normal approval processes
- Pressure for immediate payment
- Payment instructions via email only
- Multiple invoices just under approval thresholds
Communication Red Flags:
- Email addresses that don't match known vendor domains
- Unexpected payment method changes
- Urgent language designed to bypass scrutiny
- Requests to contact new phone numbers or email addresses
How Can Businesses Detect Invoice Fraud?
Early detection prevents losses and limits damage. Implement these detection methods:
Automated Invoice Matching
Deploy software like Synder or Digits that automatically matches invoices against purchase orders and delivery receipts (three-way matching). Discrepancies trigger alerts for manual review. Advanced systems use machine learning to identify anomalies in pricing, vendor behavior, and payment patterns.
Regular Vendor Audits
Conduct periodic reviews of your vendor master file. Verify that all vendors have complete, accurate information including physical addresses, multiple contact methods, and proper tax documentation. Remove inactive vendors and flag those with unusual characteristics.
Transaction Monitoring Systems
Implement real-time transaction monitoring that flags suspicious activities such as duplicate invoice numbers, payments to new vendors, changes to payment details, amounts exceeding normal ranges, and multiple invoices just under approval limits.
Segregation of Duties
Ensure no single employee can create payment processors, approve invoices, and process payments. Divide these responsibilities across multiple team members to create natural checkpoints and reduce insider fraud risk.
Periodic Reconciliation
Regularly reconcile supplier statements with internal records. Contact vendors directly using verified contact information to confirm outstanding balances and recent payments.
Practical Tip: Establish a verification protocol for any payment detail changes. Require confirmation through a secondary communication channel (phone call to known number) before processing payments to updated account information.
How Do You Prevent Invoice Fraud?
Prevention combines technology, processes, and training. Here's a comprehensive prevention strategy:
Vendor Verification and Management
Onboarding Protocol:
- Conduct thorough background checks on new vendors
- Verify business registration and tax identification
- Require multiple forms of contact information
- Visit or video conference with significant vendors
- Obtain banking information directly, never via email
Ongoing Management:
- Annual vendor recertification
- Regular updates to contact information
- Periodic spend analysis to identify unusual patterns
- Vendor risk scoring based on transaction history
Internal Controls and Approval Workflows
Multi-Level Approvals:
- Tiered approval limits based on amount and vendor type
- Required manager approval for new vendors
- Executive sign-off for high-value transactions
- Separate approvers for invoice and payment
Separation of Duties:
- Different people for vendor setup, invoice approval, and payment processing
- No single employee with end-to-end control
- Regular rotation of duties to prevent long-term schemes
Technology Solutions
Invoice Fraud Detection Software: Modern solutions use artificial intelligence to analyze invoices for fraud indicators. These systems learn normal patterns and flag anomalies including unusual vendor behavior, payment pattern changes, suspicious invoice characteristics, and duplicate or altered documents.
Secure Payment Systems:
- Multi-factor authentication for payment approvals
- Encrypted communication channels
- Automated alerts for payment detail changes
- Blockchain-based payment tracking for transparency
Email Security:
- Advanced spam and phishing filters
- Domain authentication (SPF, DKIM, DMARC)
- Email banner warnings for external communications
- Security awareness training to recognize BEC attempts
Employee Training and Culture
Regular Training Programs:
- Quarterly fraud awareness sessions
- Real-world case studies and examples
- Phishing simulation exercises
- Updates on emerging fraud tactics
Clear Reporting Channels:
- Anonymous fraud hotline
- Whistleblower protections
- Clear escalation procedures
- No-retaliation policies for good-faith reports
Practical Tip: Create a "confirmation word" system with regular vendors. When payment details change, the vendor must provide a pre-agreed verification code during phone confirmation. This simple step prevents most payment redirection fraud.
Which Industries Are Most Vulnerable to Invoice Fraud?
Certain industries face heightened invoice fraud risk due to operational characteristics:
Healthcare
Healthcare institutions process thousands of diverse invoices for medical supplies, equipment, pharmaceuticals, and services. Complex billing systems involving multiple insurers and providers create confusion that fraudsters exploit. Regulatory compliance focus sometimes overshadows fraud prevention.
Construction and Real Estate
Large projects involve dozens of contractors and suppliers with project-based relationships. Cost overruns are common and expected, making overbilling harder to detect. One-time vendor relationships reduce familiarity that might flag suspicious invoices.
Retail
Extensive supply chains with numerous vendors create opportunities for phantom suppliers and duplicate invoicing. High transaction volumes overwhelm manual verification processes. Seasonal fluctuations in ordering patterns provide cover for fraudulent invoices.
Manufacturing
Global supply chains introduce complexity with international vendors, currency exchanges, and language barriers. Multiple component suppliers for single products create verification challenges. Just-in-time manufacturing pressures rush payment approvals.
Financial Services
The irony isn't lost—financial institutions are prime targets. High trust assumptions within the industry make social engineering effective. Complex transaction structures provide camouflage for fraudulent invoices.
Education
Universities and schools handle diverse expenditures from research equipment to administrative supplies. Public funding may correlate with less rigorous oversight. Decentralized purchasing across departments creates control gaps.
Non-Profit Organizations
Limited resources often mean fewer staff and weaker internal controls. Public trust in non-profits may extend to inadequate verification. Grant-funded programs may lack sophisticated financial oversight.
Industry-Specific Tip: Recognize your industry's unique vulnerabilities and tailor controls accordingly. Construction companies should verify subcontractor licenses; healthcare organizations should validate supplier DEA numbers; retailers should confirm supplier references through industry networks.
What Are the Financial and Non-Financial Impacts of Invoice Fraud?
Invoice fraud damage extends far beyond stolen funds:
Direct Financial Losses
Immediate Costs:
- Stolen payments (averaging $125,000 per incident)
- Investigation and forensic accounting fees
- Legal costs for pursuing recovery
- Increased insurance premiums
Ongoing Costs:
- Implementation of enhanced security measures
- Hiring fraud prevention specialists
- Upgrading technology systems
- Increased audit expenses
Operational Disruptions
Fraud investigations divert resources from core business activities. Payment processes may be frozen pending investigation. Vendor relationships suffer when legitimate invoices face increased scrutiny. Employee productivity drops as teams navigate enhanced verification procedures.
Reputational Damage
News of fraud can damage stakeholder confidence. Customers question business competence. Investors become concerned about financial controls. Partners reconsider relationships with victimized companies. Recruiting talent becomes harder when fraud incidents are public.
Legal and Regulatory Consequences
Companies may face regulatory penalties for inadequate controls. Shareholders can file lawsuits alleging negligence. Directors and officers face potential personal liability. Regulatory scrutiny increases, requiring additional compliance resources.
Employee Impact
Team morale suffers, especially when fraud involves internal collusion. Trust erodes within organizations. Honest employees face increased surveillance and verification requirements. Fear and suspicion can replace collaborative culture.
Recovery Reality: Only 14% of invoice fraud losses are recovered. The remaining 86% represents permanent financial loss, making prevention exponentially more valuable than detection.
What Should You Do If You Detects Invoice Fraud?
Swift action limits damage when fraud is discovered:
Immediate Response (First 24 Hours)
- Stop Further Payments: Immediately halt any pending payments to the suspected fraudulent vendor
- Secure Evidence: Preserve all related documentation, emails, and payment records
- Notify Your Bank: Contact your financial institution to attempt payment recovery or block future fraudulent transactions
- Alert Management: Inform executive leadership and legal counsel
- Isolate Systems: If email compromise is suspected, isolate affected accounts
Investigation Phase (First Week)
- Conduct Internal Review: Determine the fraud scope, method, and entry point
- Notify Law Enforcement: File reports with local police and FBI (for BEC cases)
- Engage Forensic Experts: Consider hiring fraud investigation specialists for complex cases
- Review Vendor File: Verify all other vendors for similar indicators
- Assess Control Failures: Identify how the fraud circumvented existing controls
Recovery and Prevention (Ongoing)
- Pursue Recovery: Work with legal counsel to recover funds through civil action
- Strengthen Controls: Implement additional safeguards to prevent recurrence
- Update Policies: Revise procedures based on lessons learned
- Communicate Transparently: Inform affected vendors and stakeholders as appropriate
- Monitor for Patterns: Watch for similar attempts using different methods
Legal Tip: Document everything. Detailed records significantly improve chances of successful prosecution and insurance recovery. Include dates, times, individuals involved, exact amounts, and all communications.
How Will Invoice Fraud Evolve in the Future?
Understanding emerging threats helps businesses prepare:
AI-Powered Fraud
Artificial intelligence will enhance both fraud detection and fraud execution. Criminals will use AI to create highly convincing fake invoices, analyze payment patterns to identify vulnerabilities, generate personalized social engineering attacks, and automate large-scale fraud campaigns.
Defenders will counter with AI-powered detection systems that identify subtle anomalies invisible to human reviewers, predict fraud attempts before they occur, integrate watchlist screening, and adapt to evolving fraud tactics in real time.
Deepfake Technology
Voice and video deepfakes will authenticate fraudulent payment requests. Fraudsters may create fake video calls from executives approving payments or generate voice recordings confirming invoice changes. This technology makes social engineering dramatically more effective.
Blockchain and Cryptocurrency
Decentralized finance introduces new fraud vectors while offering potential solutions. Smart contract vulnerabilities may be exploited for fraudulent payments. However, blockchain's transparency and immutability could revolutionize invoice verification and payment tracking.
Increased Insider Threats
As external defenses strengthen, insider threats will increase. Financial pressures, remote work isolation, and sophisticated recruitment by criminal organizations will drive more internal fraud. Employee financial wellness programs and psychological support may become fraud prevention tools.
Quantum Computing Risks
Future quantum computers could break current encryption standards, potentially exposing financial communications. Organizations must prepare for post-quantum cryptography to maintain payment security.
Preparation Strategy: Build adaptable fraud prevention programs focused on principles rather than specific techniques. Invest in scalable technology platforms that can evolve. Foster a culture where fraud awareness is continuous, not periodic.
Frequently Asked Questions About Invoice Fraud
What is the most common type of invoice fraud?
Business email compromise (BEC) is currently the most common and costly invoice fraud type, involving hacked or spoofed email accounts to redirect payments. Fake invoice fraud and duplicate invoicing are also prevalent, particularly targeting small businesses with limited verification processes.
How can I verify if an invoice is legitimate?
Contact the vendor directly using previously verified contact information—never use contact details from the suspicious invoice. Verify the invoice matches a purchase order, check that the vendor exists in your approved vendor list, confirm payment details haven't changed, and validate that services or products were actually delivered.
What should I do if I accidentally paid a fraudulent invoice?
Immediately contact your bank to attempt recovery or block additional fraudulent charges. File a police report and notify the FBI's Internet Crime Complaint Center for BEC cases. Preserve all evidence including emails and payment records. Engage legal counsel to explore recovery options. Alert other vendors about potential compromise.
Are small businesses more vulnerable to invoice fraud?
Yes. Small businesses typically have fewer resources for sophisticated fraud detection systems, less segregation of duties due to smaller staff, limited fraud awareness training, and weaker cybersecurity measures. However, they can still implement effective prevention through basic controls and vigilance.
How do criminals get my vendor information to create fake invoices?
Fraudsters obtain vendor information through data breaches and dark web purchases, social media research on vendor relationships, public business records and databases, phishing attacks on employees, and insider information from dishonest employees.
Can invoice fraud be covered by insurance?
Some insurance policies cover invoice fraud under crime insurance, cyber insurance, or fraud insurance provisions. However, coverage varies significantly by policy. Review your insurance carefully and consider specialized fraud insurance if your current policy has gaps. Many policies exclude social engineering fraud unless specifically added.
What are the legal consequences for committing invoice fraud?
Invoice fraud is a federal crime punishable by fines and imprisonment. Wire fraud carries up to 20 years in federal prison. Mail fraud has similar penalties. Many states have additional fraud statutes. Civil liability can result in restitution orders requiring full repayment plus damages and interest.
How can I train employees to recognize invoice fraud?
Conduct quarterly fraud awareness training sessions with real case studies. Run simulated phishing exercises to test recognition skills. Create easy reference guides highlighting red flags. Establish clear reporting procedures with no-blame policies for good-faith reports. Make fraud prevention part of onboarding for all new hires.
What technology can help prevent invoice fraud?
Automated invoice matching systems, AI-powered fraud detection software, secure payment platforms with multi-factor authentication, advanced email security with BEC protection, blockchain-based vendor verification, and automated reconciliation tools all provide technological fraud prevention layers.
How long does it typically take to recover from invoice fraud?
Financial recovery rarely exceeds 14% of lost funds. Operational recovery takes 3-6 months to restore normal payment processes and rebuild vendor trust. Reputational recovery can take years depending on public disclosure and company response. Full organizational recovery including strengthened controls typically takes 6-12 months.
Key Takeaways: Protecting Your Business from Invoice Fraud
Invoice fraud represents a growing threat in our increasingly digital business environment. While technology has created new vulnerabilities, it also provides powerful tools for detection and prevention.
The most effective defense combines technology, processes, and people. Automated systems catch what humans miss. Strong internal controls create necessary checkpoints. Well-trained, vigilant employees serve as your first line of defense.
Success requires viewing fraud prevention not as a one-time project but as an ongoing commitment. Fraudsters constantly evolve their tactics, so your defenses must evolve too. Regular training, periodic control reviews, and continuous improvement of detection systems keep your organization protected.
Remember that perfect security is impossible. The goal is to make your organization a harder target than the next company. Strong controls, consistent vigilance, and quick response when fraud occurs will protect your business from the vast majority of invoice fraud attempts.
Final Action Steps:
- Audit your current vendor verification and invoice approval processes this week
- Implement three-way matching if not already in place
- Schedule quarterly fraud awareness training for all employees
- Review and strengthen payment approval workflows
- Establish verification protocols for any payment detail changes
By taking proactive measures today, you protect your organization's financial health, operational stability, and reputation for years to come.
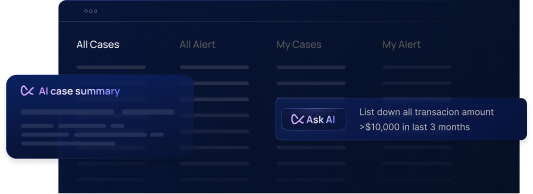
Flagright provides advanced fraud prevention solutions designed specifically for modern businesses facing invoice fraud and payment scams. Our AML compliance solution detects fraudulent invoices in real time, protecting your organization from costly losses, with built-in case management and AI forensics to help investigate, document, and resolve alerts faster. Learn more about our fraud detection solutions.




.svg)






.webp)