AT A GLANCE
Ghost Tap is an emerging relaying NFC payment data to a distant point-of-sale, add them to mobile wallets, and use two smartphones to relay tap-to-pay signals across distances—even continents—to make fraudulent purchases. Detection requires analyzing metadata like device IDs, geolocation mismatches, entry mode inconsistencies, and transaction velocity patterns in real time to expose the subtle differences between legitimate taps and relayed fraud. Watchlist screening adds another layer of protection by flagging known high-risk entities.
What is an NFC Relay Attack?
An NFC relay attack intercepts and extends the communication range between a contactless card or mobile wallet and a payment terminal by routing the signal through proxy devices over longer distances than normal NFC allows.
In a standard contactless transaction, Near Field Communication works only within a few centimeters. NFC relay attacks break this limitation by capturing the NFC signal from a victim's card or phone and transmitting it in real-time—potentially across cities or even countries—to another device that completes the transaction at a point-of-sale terminal.
The attack works by positioning a rogue NFC reader near the victim's contactless card (which could be in their pocket or wallet) to activate and capture the card's signal. This captured data is instantly relayed over the internet to an accomplice's device configured to act as an NFC emulator. That second device then communicates with a legitimate payment terminal as if the actual card were present, completing the transaction while the victim remains unaware.
These attacks are particularly dangerous because they produce transactions that appear completely legitimate to payment systems. The cryptographic tokens are valid, the card credentials check out, and the transaction looks like a normal tap-to-pay purchase. Only deeper analysis of contextual metadata reveals the fraud.
How Does Ghost Tapping Work?
Ghost Tap attacks unfold in multiple coordinated stages involving credential theft, mobile wallet provisioning, and real-time NFC relay between two devices controlled by fraudsters.
Stage 1: Stealing Card Credentials and OTPs
Attackers first obtain the victim's card details and any one-time passwords needed to add the card to a digital wallet. This typically happens through mobile malware that captures card data stored on the victim's phone and intercepts SMS authentication codes, or through sophisticated phishing campaigns that trick victims into providing card information and verification codes.
Stage 2: Provisioning the Stolen Card
Once criminals have the necessary credentials, they add the victim's card to their own mobile wallet—Apple Pay, Google Pay, or similar services. The wallet generates a device-specific token representing the card. This tokenized credential is what makes the attack particularly insidious: the token is legitimate and authorized by the issuer, so transactions using it pass standard fraud checks.
Stage 3: Setting Up the NFC Relay
Rather than using the compromised wallet directly (which would create a direct connection between their device and the crime), attackers establish a relay system using tools like NFCGate. The attacker's phone holding the stolen card token acts as an NFC reader, capturing the payment signal. This signal is transmitted over the internet to a second device held by a “money mule".
Stage 4: Executing the Fraudulent Transaction
The accomplice's phone, running compatible relay software, emulates the victim's card token to the store's point-of-sale terminal. When the accomplice taps their phone at checkout, they're actually relaying the victim's legitimate card credentials from the first device. To the merchant and payment processor, it appears as a normal contactless transaction from an authorized card.
This relay can happen across any distance. The attacker's device with the stolen token could be in one country while the accomplice makes purchases in another, all happening in real-time with transaction completion times of just seconds.
Common Attack Variations
Point-of-sale spoofing involves fraudsters setting up fake or tampered merchant terminals that route transactions remotely. Some organized fraud rings register fraudulent merchant POS devices under mule identities, making stolen card transactions appear as normal retail sales.
Stolen token replay attacks leverage mobile wallet credentials to rapidly purchase easily resellable items like gift cards or electronics at multiple stores before issuers block the compromised token. Attackers maximize value through high-velocity purchasing sprees.
Advanced techniques include manipulating ATM or POS software (such as the Track2NFC exploit) to force offline transaction approvals, bypassing standard authorization checks that might detect anomalies.
How Long Does an NFC Relay Attack Take?
NFC relay attacks happen extremely quickly, typically completing in just 0.5 to 3 seconds from signal capture to transaction authorization—fast enough that victims and merchants have no opportunity to detect the relay in progress.
The speed depends on several factors. Network latency between the two relay devices affects total duration, with local high-speed internet enabling faster relays than connections with higher ping times. The NFC communication itself is nearly instantaneous, taking only milliseconds to read card data and transmit payment credentials.
Transaction processing time at the point-of-sale varies but typically completes within 1-2 seconds for contactless payments. The relay adds minimal overhead—usually just 100-500 milliseconds depending on connection quality—making the overall transaction timing nearly identical to legitimate contactless taps.
This speed makes real-time detection critical. By the time a transaction is flagged for manual review, the fraudulent purchase has already been approved and the criminals have moved on to the next target. Only automated systems analyzing metadata in milliseconds can intervene before authorization completes.
What Metadata Signals Reveal NFC Relay and Ghost Tap Fraud?
While Ghost Tap attacks mimic legitimate contactless payments on the surface, multiple metadata signals can expose the underlying fraud when analyzed together in real-time.
POS Entry Mode Inconsistencies
Every card transaction includes an entry mode code indicating how the card data was obtained: EMV chip, contactless NFC, magnetic stripe, or e-commerce entry. For contactless transactions, this is typically code 07 or 91. Fraudsters sometimes generate inconsistencies here—for example, a transaction flagged as contactless when the account isn’t known to use contactless, or a supposed EMV chip transaction that actually contains magnetic stripe data.
Issuers should verify that entry modes align with the customer's known payment methods and expected usage channels. A customer who only uses physical chip cards suddenly showing contactless transactions from a mobile wallet they never registered represents a clear fraud signal. Similarly, contactless-MSD (magnetic stripe data via contactless) on EMV-only cards reveals potential relay or cloning attempts.
Unfamiliar Device Identifiers
Digital wallet transactions tie to specific device identifiers including device account numbers and wallet IDs. When a transaction originates from a device the system has never seen associated with that customer or card, it signals potential account takeover or Ghost Tap fraud.
Tracking device fingerprints across transaction history creates a baseline of known, trusted devices. A card suddenly being used via a new phone—particularly when the customer's primary device shows no recent wallet activity—indicates an attacker has added the card to their own device. This signal becomes even stronger when combined with geographic or behavioral anomalies.
IP Address and Geolocation Mismatches
Even card-present transactions can carry network metadata revealing location discrepancies. When available, fraud systems should compare the merchant's physical location against the device's IP geolocation and the customer's known addresses or recent activity patterns.
A stark mismatch—such as a tap-to-pay transaction at a merchant in London while the cardholder's authenticated app session shows them in Berlin—strongly suggests an NFC relay attack. Similarly, transactions routing through unusual IP addresses including proxies, VPNs, or addresses from high-risk regions should trigger additional scrutiny.
Geolocation analysis proves particularly effective because legitimate contactless transactions occur on local networks near the merchant. When the digital wallet device's IP resolves to a different country than where the physical tap occurred, a relay is almost certainly in play.
Merchant Category and Velocity Anomalies
Behavioral context around merchant activity reveals Ghost Tap patterns. Fraudsters typically execute burst attacks, making multiple rapid transactions to maximize stolen card value before detection and blocking occurs. Real-time risk scoring using velocity and transaction clustering enables earlier detection and faster intervention.
Merchant velocity rules flag unusual patterns such as five or more transactions at the same merchant within ten minutes, multiple back-to-back purchases at different merchants in a short timespan, or sudden spikes in transaction count or value at merchants the customer rarely visits. A normally low-velocity merchant processing a rapid series of identical-card taps likely indicates either a compromised POS device or a mule executing a cash-out operation.
Industry-specific patterns matter too. High-value goods merchants (electronics, jewelry, gift cards) seeing rapid repeat taps from the same card should trigger alerts, as these match known Ghost Tap targeting preferences for easily resellable items.
Time-of-Day and Session Context Irregularities
Analyzing transaction timing against customer behavioral patterns exposes temporal anomalies. Ghost Tap cash-out operations often cluster in off-hours or occur immediately after a card is provisioned to a new wallet.
A card that has never been used at 2 AM suddenly showing multiple tap-to-pay transactions during that timeframe represents a clear deviation from normal behavior. This signal strengthens when combined with session data: was the legitimate cardholder's mobile banking app active during the transaction? Was their known device connected to networks, or was it offline or in airplane mode?
In Ghost Tap scenarios, attackers sometimes place their relay device in airplane mode while transmitting NFC data, making the actual cardholder's device location and connectivity status unknown. Transactions occurring when the customer's authenticated device shows no network connectivity suggest the tap came from a different device entirely.
What Tools Can Detect Digital Skimming and NFC Fraud in Real Time?
Real-time fraud detection systems use multiple technological capabilities to identify NFC relay and Ghost Tap attacks as they happen, continuously monitoring granular metadata and applying real-time rules.
IP and Device Intelligence Platforms
Advanced fraud prevention platforms automatically resolve IP addresses to physical geolocations and enrich them with reputational data. These systems identify when transactions route through anonymizing services, VPNs, proxy servers, or IP addresses flagged for previous fraud activity.
Device fingerprinting creates unique identifiers for each phone, tablet, or computer accessing payment systems. By tracking device IDs across transactions, platforms build profiles of trusted devices and flag when unfamiliar devices attempt to use customer credentials. This proves critical for detecting Ghost Tap attacks where stolen cards appear on new, unrecognized devices.
Transaction Metadata Analysis Engines
Sophisticated fraud systems parse and analyze dozens of transaction attributes in real-time, including POS entry mode codes, merchant category codes, transaction amounts, timestamps, authorization response codes, and network routing information. These engines compare each transaction against the customer's historical baseline to identify deviations indicating fraud.
Machine learning models process these metadata signals to calculate composite fraud scores. Rather than relying on single indicators, they identify patterns where multiple subtle anomalies align—such as a contactless transaction from a new device, in an unexpected location, at an unusual merchant type, during off-hours.
Dynamic Rules Engines
No-code rules engines empower fraud teams to build complex detection logic combining multiple conditions without requiring engineering resources. These platforms support threshold checks, pattern matching with regular expressions, geofencing rules, velocity limits, and multi-dimensional filtering across customer profiles, transaction types, time windows, and geographic regions.
Rules can layer multiple conditions to create precise targeting. For example: "If transaction type equals NFC AND device not in customer's known device history AND IP country differs from merchant country AND transaction occurs between midnight and 5 AM, then flag for review." This surgical precision catches specific fraud patterns while minimizing false positives on legitimate transactions.
Real-Time Monitoring and Alerting Systems
Continuous monitoring platforms track every transaction as it flows through payment networks, applying fraud rules and scoring models before authorization decisions are made. When suspicious patterns emerge, automated alerts route to fraud analysts with complete transaction context, customer history, and recommended actions.
The critical factor is speed. Ghost Tap attackers operate at internet velocity, completing fraudulent transactions in seconds. Only real-time systems analyzing transactions during the authorization flow can intervene quickly enough to prevent losses.
How Does Flagright Detects Ghost Tap and NFC Relay Attacks?
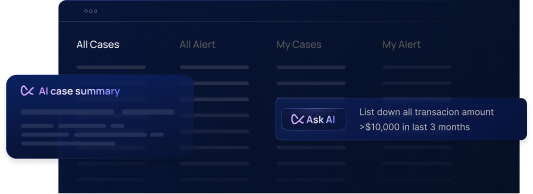
Flagright's fraud prevention platform combines deep metadata analysis with a powerful no-code rules engine to identify sophisticated contactless payment fraud as it happens.
Comprehensive IP and Device Intelligence
Flagright automatically enriches every transaction with IP geolocation data and device reputation information. When a supposedly in-store NFC transaction from a German merchant actually routes through an IP address in another country, the platform immediately flags this geographic inconsistency—since legitimate contactless taps at physical point-of-sale locations should originate from local networks near the merchant.
The system tracks device identifiers across transactions to build comprehensive profiles of known, trusted devices associated with each customer and card. When a card suddenly appears on an unfamiliar device, particularly one with suspicious characteristics or a history of fraud, Flagright surfaces this anomaly for investigation or automatic blocking.
Advanced Rules Engine for Multi-Signal Analysis
Flagright's no-code rules engine enables fraud teams to create sophisticated detection logic without writing code. The platform supports complex Boolean logic, regular expression pattern matching, threshold-based triggers, time-window analysis, and cross-attribute comparisons—all configured through an intuitive interface.
Teams can build layered rules that combine multiple metadata signals into precise fraud indicators. Rather than relying on single data points, rules require that several anomalies align before triggering, which dramatically improves precision by catching actual fraud while reducing false positives on unusual but legitimate transactions.
For example, a rule might specify: "Transaction entry mode is contactless NFC AND device ID not in customer's known device history AND IP country differs from merchant country AND transaction amount exceeds customer's average by 200% → Block transaction and alert fraud team." This multi-dimensional approach catches Ghost Tap attacks that would slip past simpler single-factor checks.
Behavioral Pattern Recognition
The platform continuously learns normal patterns for each customer, merchant, and transaction type. This behavioral baseline makes anomalies stand out clearly. A customer who typically makes two transactions per week suddenly showing ten transactions in an hour triggers velocity rules. A card never used for contactless payments suddenly tapping at multiple locations in quick succession signals potential Ghost Tap activity.
Flagright enables teams to set dynamic thresholds based on customer risk profiles, transaction types, time of day, and other contextual factors. High-risk scenarios trigger stricter rules while low-risk activity flows through with minimal friction, optimizing both fraud prevention and customer experience.
Real-Time Processing and Response
All analysis happens in real-time during transaction authorization. The moment a payment request enters the system, Flagright evaluates it against active rules, scores it for fraud risk, and can automatically block suspicious transactions before they're approved. For borderline cases, transactions are flagged for rapid manual review with full context provided to analysts.
This speed is essential for combating Ghost Tap attacks. Fraudsters execute rapid bursts of transactions to maximize value before detection. Only systems that analyze and respond in milliseconds can effectively stop these attacks before significant losses occur.
Example Rules for Detecting NFC Relay and Ghost Tap Fraud
Effective fraud detection rules combine multiple metadata conditions to identify specific attack patterns with high precision.
Rule 1: Unknown Device with Geographic Mismatch
IF transaction.entry_mode == "NFC contactless"
AND transaction.device_ID NOT IN customer.known_devices
AND IP_geolocation.country != merchant.country
THEN flag_for_review AND require_step_up_authentication
Rationale: This rule catches cases where a contactless tap originates from an unfamiliar device and shows a network location mismatch between the device IP and merchant location. Legitimate card taps at stores use familiar devices and local networks. When both signals diverge, it strongly indicates an NFC relay or cloned device scenario. The rule triggers enhanced verification rather than immediate blocking to account for legitimate edge cases like international travelers.
Rule 2: High-Velocity Merchant Activity
IF merchant.category IN ["electronics", "jewelry", "gift_cards"]
AND COUNT(transactions) >= 5 within 10_minutes
AND transaction.card_ID == same_card
THEN flag_for_review AND temporarily_suspend_card
Rationale: Ghost Tap operations leave velocity fingerprints. Fraudsters run numerous transactions quickly to maximize stolen card usage before detection. Brick-and-mortar merchants in high-value categories rarely see the same card tapped repeatedly in minutes. This rule spotlights burst activity patterns characteristic of cash-out operations, particularly at merchants selling easily resellable goods.
Rule 3: Off-Hours Activity with New Wallet
IF transaction.time BETWEEN 23:00 AND 05:00
AND wallet.provisioning_date < 48_hours
AND transaction.entry_mode == "NFC contactless"
AND customer.historical_contactless_usage == false
THEN block_transaction AND alert_fraud_team
Rationale: Temporal and behavioral anomalies compound to create strong fraud signals. A customer who never used contactless payments suddenly showing NFC transactions in the middle of the night from a newly provisioned wallet matches the Ghost Tap attack pattern. This combination warrants immediate blocking and investigation.
Rule 4: Entry Mode Inconsistency
IF transaction.entry_mode == "contactless_MSD"
AND card.chip_capability == "EMV_only"
THEN block_transaction
Rationale: Contactless transactions should use EMV cryptograms, not magnetic stripe data (MSD). When a chip card shows contactless-MSD entry mode, it indicates potential relay misuse, cloning, or technical manipulation. This strict rule blocks obvious inconsistencies that represent clear fraud or compromise.
Rule 5: Impossible Travel Velocity
IF time_between_transactions < 30_minutes
AND distance_between_merchants > 50_miles
AND transaction.entry_mode IN ["NFC contactless", "EMV chip"]
THEN flag_for_review
Rationale: Physical cards and phones cannot teleport. When the same card appears at widely separated locations within a timeframe that makes physical travel impossible, it signals cloning, relay attacks, or multiple fraudulent devices. This rule catches both Ghost Tap and traditional card cloning schemes.
These examples demonstrate how combining weak individual signals into composite rules creates powerful fraud detection. Flagright's rules engine makes implementing such complex logic straightforward, allowing fraud teams to model attack patterns and deploy countermeasures rapidly as new threats emerge.
How to Prevent Ghost Tapping
Financial institutions can implement multiple strategies to prevent Ghost Tap and NFC relay attacks from succeeding against their customers and payment systems.
Implement Strong Multi-Factor Authentication
Require robust authentication when adding cards to mobile wallets, including biometric verification, device binding to known trusted devices, and out-of-band confirmation through authenticated channels. Make it difficult for attackers to provision stolen credentials by requiring verification steps they cannot easily compromise.
Deploy Real-Time Transaction Monitoring
Implement fraud detection systems that analyze transaction metadata in real-time, applying sophisticated rules that evaluate device fingerprints, IP geolocation, entry mode codes, merchant patterns, and velocity indicators before authorizing transactions. Speed is critical—detection must occur during authorization, not after losses have occurred.
Enable Behavioral Analytics
Build customer behavior baselines that track normal transaction patterns, device usage, geographic activity, and temporal habits. Use machine learning to identify deviations that signal account takeover or fraudulent device usage. Behavioral models excel at detecting subtle changes that rule-based systems might miss.
Require Step-Up Authentication for Anomalies
When transactions show suspicious characteristics but don't definitively prove fraud, require additional verification such as one-time passwords, push notification approval, biometric confirmation, or security questions. This adds friction for attackers while allowing legitimate customers to complete unusual but valid transactions.
Implement Velocity and Amount Limits
Set dynamic transaction limits based on customer risk profiles and behavior patterns. High-velocity activity or unusually large transactions trigger automatic holds or denials, preventing attackers from executing rapid cash-out operations before detection.
Educate Customers on Mobile Wallet Security
Inform customers about Ghost Tap risks and preventive measures including enabling wallet lock features, using biometric authentication, monitoring account activity regularly, and reporting suspicious wallet additions immediately. Customer awareness creates an additional defense layer.
Monitor for Wallet Provisioning Anomalies
Track when cards are added to new mobile wallets and apply extra scrutiny to transactions from recently provisioned wallets. Require confirmation when cards are added to devices from unusual locations or to multiple wallets in short timeframes.
Frequently Asked Questions About NFC Relay and Ghost Tap Attacks
What is the difference between Ghost Tap and regular NFC relay attacks?
Ghost Tap is a specific type of NFC relay attack focused on mobile wallets. Regular NFC relay attacks intercept signals from physical contactless cards, while Ghost Tap involves stealing card credentials to provision them in the attacker's mobile wallet, then relaying those wallet tokens to complete fraudulent transactions. Ghost Tap bridges card-present and card-not-present fraud by using stolen digital credentials rather than physical cards.
How quickly can an NFC relay attack happen?
NFC relay attacks complete in 0.5 to 3 seconds from initial signal capture to transaction authorization. The actual NFC communication takes milliseconds, network relay adds 100-500 milliseconds depending on connection quality, and POS processing completes within 1-2 seconds. This speed makes real-time automated detection essential since manual review cannot occur fast enough to prevent authorization.
Can ghost tapping be detected by banks?
Yes, banks can detect Ghost Tap attacks by analyzing transaction metadata including unfamiliar device IDs, IP address mismatches between device location and merchant location, unusual velocity patterns, off-hours activity, entry mode inconsistencies, and deviations from customer behavioral baselines. Advanced fraud detection systems combine these signals in real-time to identify and block suspicious transactions.
What is NFCGate and how is it used in Ghost Tap attacks?
NFCGate is an open-source research tool that enables NFC relay capabilities. Attackers use it to capture NFC payment signals from one device and transmit them over the internet to a second device that emulates the original card to a point-of-sale terminal. While developed for security research, criminals have weaponized it for Ghost Tap fraud operations.
How do fraudsters get card details for Ghost Tap attacks?
Attackers obtain card credentials through mobile malware that captures stored card data and intercepts SMS one-time passwords, phishing campaigns that trick victims into providing card information and verification codes, database breaches that expose payment card data, or social engineering attacks targeting customer service representatives to authorize wallet provisioning.
What are contactless-MSD transactions?
Contactless-MSD (Magnetic Stripe Data) transactions use magnetic stripe card data transmitted via NFC rather than proper EMV chip cryptography. Modern chip-enabled cards should only perform contactless transactions using EMV protocols. When a contactless-MSD transaction appears for an EMV-capable card, it signals potential cloning, relay attacks, or terminal manipulation.
Can Ghost Tap attacks work internationally?
Yes, Ghost Tap attacks work across any distance. The attacker's device holding stolen card tokens can be in one country while accomplices make purchases in another country or even on different continents. The relay happens over the internet in real-time, making geographic distance irrelevant to the attack's technical success.
How do velocity rules help detect Ghost Tap fraud?
Velocity rules detect unusual transaction frequency patterns characteristic of Ghost Tap cash-out operations. Fraudsters typically execute multiple rapid transactions to maximize value before the card is blocked. Rules are fully customizable, purchases at multiple merchants in short timeframes, or sudden spikes in daily transaction counts catch these burst patterns.
What is a POS entry mode code?
The POS entry mode code indicates how card data entered the payment system: EMV chip contact, contactless NFC, magnetic stripe swipe, manual key entry, or e-commerce. Entry mode 07 or 91 typically indicates contactless NFC transactions. Fraud systems analyze entry modes for inconsistencies like contactless transactions from accounts without mobile wallet provisioning or contactless-MSD on EMV-only cards.
Can tap-to-pay be hacked while the card is in my wallet?
Traditional NFC skimming from pockets is difficult because NFC range is very limited (typically under 4 centimeters). However, Ghost Tap attacks don't require proximity to your physical card—they steal your card credentials digitally to add them to the attacker's mobile wallet. The relay attack then occurs between the attacker's devices, not by reading your card directly.
How is Ghost Tap different from traditional credit card fraud?
Traditional credit card fraud uses stolen card numbers for card-not-present transactions or creates physical counterfeit cards. Ghost Tap uses stolen credentials to provision legitimate mobile wallets, generating valid device tokens that produce card-present contactless transactions. This makes Ghost Tap harder to detect since transactions carry proper cryptographic credentials and appear as normal taps.
What tools provide real-time contactless transaction tracking?
Enterprise fraud prevention platforms like Flagright, SEON, and other specialized AML compliance solutions provide real-time transaction monitoring with metadata analysis, device fingerprinting, IP intelligence, behavioral analytics, and customizable rules engines. These systems analyze transactions during authorization to detect and block fraud before it completes.
How can merchants identify fake contactless payment readers?
Merchants should inspect payment terminals for physical tampering, unusual attachments, or devices placed over card readers. Verify terminals match the expected model and branding from their payment processors. Regularly check for firmware integrity and unusual network connections. However, Ghost Tap attacks typically use legitimate terminals with relay happening on the customer side, so merchant-side detection is limited.
Does relay allow tap-to-pay with its debit cards?
This question appears to reference a specific fintech company called Relay. For accurate information about Relay's specific product features, tap-to-pay support, fraud protection policies, and security measures, users should consult Relay's official documentation or contact their customer support directly.
What is the best solution for ghost terminal fraud?
Comprehensive fraud prevention requires multi-layered approaches: real-time transaction monitoring systems analyzing metadata, behavioral analytics establishing customer baselines, device intelligence tracking known and unknown devices, dynamic rules engines combining multiple fraud signals, step-up authentication for suspicious transactions, and customer education about mobile wallet security. No single tool provides complete protection—effective defense requires integrated systems.
Key Tips for Protecting Against NFC Relay and Ghost Tap Fraud
Tip 1: Monitor device provisioning events closely. Track when cards are added to new mobile wallets and apply enhanced scrutiny to transactions from recently provisioned devices. Require out-of-band confirmation for wallet additions from unfamiliar devices or locations.
Tip 2: Implement impossible travel detection. Flag transactions when the same card appears at geographically distant locations within timeframes that make physical travel impossible. This catches both relay attacks and cloned cards.
Tip 3: Combine multiple weak signals into strong rules. Individual metadata anomalies may be explainable, but multiple simultaneous anomalies—unfamiliar devices plus geographic mismatch plus unusual timing—create high-confidence fraud indicators.
Tip 4: Focus on velocity patterns. Ghost Tap operations leave distinctive footprints through rapid transaction sequences. Set merchant-specific velocity thresholds that flag burst activity exceeding normal patterns for that business type.
Tip 5: Validate entry mode consistency. Verify that transaction entry modes match card capabilities and customer provisioning. Block contactless-MSD on EMV cards and flag contactless transactions for customers who never enabled mobile wallets.
Tip 6: Analyze temporal patterns. Off-hours activity, transactions immediately after wallet provisioning, and deviations from customer time-of-day habits all signal potential fraud worthy of additional verification.
Tip 7: Leverage IP intelligence. Geographic mismatches between device IP locations and merchant locations strongly indicate relay attacks. Enrich transactions with IP reputation data to identify VPNs, proxies, and anonymization services.
Tip 8: Build behavioral baselines. Establish normal patterns for each customer across merchants, amounts, frequency, locations, and times. Machine learning models excel at detecting subtle deviations from these baselines that rule-based systems might miss.
Tip 9: Require step-up authentication for high-risk scenarios. When multiple fraud signals align but don't conclusively prove fraud, use additional verification methods to confirm the legitimate customer authorized the transaction without blocking valid activity.
Tip 10: Update rules continuously. Fraud patterns evolve as attackers adapt to defenses. Regularly review fraud data, test new rule configurations, and deploy updated detection logic to stay ahead of emerging Ghost Tap tactics.
Conclusion
NFC relay attacks and Ghost Tap fraud represent sophisticated threats that exploit the trust and convenience of contactless payments. By stealing card credentials and mobile wallet tokens, then using relay technology to transmit payment signals across any distance, criminals execute fraudulent transactions that appear completely legitimate on the surface.
The key to detecting these attacks lies in analyzing transaction metadata that surface-level checks miss. POS entry mode inconsistencies, unfamiliar device fingerprints, IP address and geolocation mismatches, unusual merchant velocity patterns, and temporal anomalies all provide signals that, when combined, expose relay attacks despite their valid cryptographic credentials.
Financial institutions must implement real-time fraud detection systems capable of analyzing multiple metadata signals simultaneously, applying sophisticated rules during transaction authorization, and routing flagged activity into case management workflows for investigation. The speed of Ghost Tap attacks—completing in just seconds—demands automated systems that can identify and block fraud before authorization completes.
Platforms like Flagright provide the comprehensive capabilities needed to combat these threats, including deep IP and device intelligence, AI forensics, powerful no-code rules engines for creating multi-signal detection logic, and behavioral analytics that identify deviations from customer patterns. Real-time processing helps stop fraud as it happens rather than discovering it after losses occur.
As contactless payments continue growing and fraudsters develop increasingly sophisticated attack techniques, the financial industry must adopt metadata-driven, real-time fraud detection to it’s a must for protecting customers, remittances, and payment ecosystems. The future of fraud prevention lies not in analyzing what transactions say they are, but in understanding the context that reveals what they actually are.
Contact Flagright to schedule a demo and see how real-time rules and comprehensive transaction intelligence can protect your institution and customers from emerging contactless payment fraud.




.svg)