AT A GLANCE
Transaction monitoring rules are automated criteria that flag suspicious financial activity for AML compliance. Effective rules combine regulatory requirements with risk-based approaches, using AI and machine learning to reduce false positives while catching genuine threats. This guide covers how to develop, customize, and test monitoring rules that protect your institution while meeting regulatory standards from FinCEN, MAS, and other global bodies.
Why Is Transaction Monitoring Critical for Financial Institutions?
Transaction monitoring protects the global financial system from criminal exploitation. It is estimated that money laundered globally in one year ranges from 2% to 5% of global GDP, amounting to $800 billion to $2 trillion. Without effective monitoring, financial institutions become unwitting accomplices to money laundering, terrorism financing, and fraud.
Financial crimes are evolving rapidly, and regulatory frameworks worldwide are tightening in response. Transaction monitoring is no longer just a compliance checkbox; it's an essential case management strategy that affects your institution's ability to operate in a regulated industry. Failure to implement effective monitoring can result in severe penalties, substantial fines, and irreparable reputational damage.
What Is Transaction Monitoring in AML Compliance?
Transaction monitoring is the systematic process of reviewing customer transactions—either in real-time or post-transaction—to identify suspicious patterns that may indicate financial crimes.
Banks, fintechs, and financial institutions use automated systems to monitor transactions continuously. These systems apply pre-configured rules and machine learning algorithms to detect activities that deviate from established baselines for customer behavior.
What Does Transaction Monitoring Accomplish?
Transaction monitoring serves three critical purposes:
- Detects and prevents financial crime: Identifies unusual patterns that may signal fraud, money laundering, terrorism financing, or other illegal activity before they cause harm
- Enhances customer behavior understanding: Analyzes transaction data to understand how customers use products and services, informing risk management and business strategy
- Ensures regulatory compliance: Meets requirements from regulatory bodies like FinCEN, MAS, and FATF while protecting your institution from penalties
What Regulatory Requirements Govern Transaction Monitoring?
Transaction monitoring regulations form a complex global framework designed to combat money laundering and terrorism financing. Understanding these requirements is the foundation for developing effective monitoring rules.
Which Regulatory Bodies Set Transaction Monitoring Standards?
Global regulatory bodies enforce different rules, but all share the goal of preventing financial crime:
Financial Crimes Enforcement Network (FinCEN): Establishes AML standards for US financial institutions under the Bank Secrecy Act (BSA) in the United States. FinCEN requires institutions to safeguard and file reports on financial transactions to support criminal, tax, and regulatory investigations.
Financial Action Task Force (FATF): Sets international standards for combating money laundering and terrorism financing. Financial Action Task Force (FATF) establishes guidelines and recommends financial institutions adopt risk-based approaches to AML/CFT measures, including transaction monitoring.
Monetary Authority of Singapore (MAS): Serves as Singapore’s central bank and financial regulatory authority, enforcing rigorous AML/CFT regulations across banking, insurance, and financial services through the MAS.
Securities and Exchange Commission (SEC): Provides guidance on AML laws, regulations, and directives applicable to broker-dealers through SEC oversight.
European Union (EU): Creates directives strengthening coordination against serious crime and terrorism. Directive (EU) 2019/1153 requires law enforcement to have direct access to bank account holder information in national centralized registries.
International Monetary Fund (IMF): Addresses financial integrity concerns in lending, capacity development, and monitoring through IMF programs, influencing AML/CFT policies globally.
What Are the Essential Regulations Impacting Transaction Monitoring?
Bank Secrecy Act (BSA): Requires US financial institutions to maintain records and file reports on currency transactions linked to illegal activity. Banks must preserve transaction trails that aid investigations.
USA PATRIOT Act: Established protocols to detect, identify, and prosecute those engaged in terrorism financing and money laundering. It increases the BSA's jurisdiction and strengthens anti-money laundering measures.
Anti-Money Laundering Act of 2020 (AMLA): Mandates the Secretary of the Treasury to examine BSA rules and make necessary adjustments to improve efficiency and effectiveness, as mandated under AMLA.
EU Directive 1153: Accelerates criminal investigations by giving law enforcement immediate access to bank account holder information through national centralized registers.
Suspicious Activity Reporting (SAR): Federal regulations require banks, fintechs, and financial institutions to file SARs with specific requirements about transaction types and criminal offenses.
How Do You Develop Effective Transaction Monitoring Rules?
Developing effective transaction monitoring solutions rules requires balancing regulatory compliance with your organization's specific risk profile. The most successful rules are neither too broad (creating alert fatigue) nor too narrow (missing genuine threats).
How Do You Align Rules with Regulatory Requirements and Business Needs?
Start by understanding your regulatory framework. Thorough research standards set by applicable bodies like Financial Conduct Authority (FCA), Financial Crimes Enforcement Network (FinCEN), and Monetary Authority of Singapore (MAS) Your rules must meet these requirements to keep your institution compliant and protect against reputational risk.
Next, evaluate your business specifics. A fintech focused on digital payments requires different monitoring parameters than a traditional bank offering diverse financial services. Consider your customer base, product offerings, and transaction types. Understanding these operational details enables you to create rules that detect suspicious activity effectively across all payment types and remittances.
How Do You Customize Rules for Different Customer Segments?
A risk-based approach is essential. This means customizing monitoring criteria to match the risk profiles of different customer segments.
High-risk customers—those engaged in large-value transactions or located in high-risk countries—need more thorough monitoring and additional verifications. Low-risk customers can have more relaxed thresholds without compromising compliance.
Leverage data from Customer Due Diligence (CDD) processes. This data provides insights into normal transaction patterns, helping you set appropriate thresholds and parameters that trigger alerts for unusual activities.
For higher-risk customers, incorporate enhanced due diligence (EDD) measures into your rules. Set tighter transaction thresholds, conduct more frequent reviews, and apply more complex indicators of suspicious activity. This focused approach improves detection rates for genuine threats while reducing false positives from legitimate transactions.
What Are Common Transaction Monitoring Rules Examples?
Effective transaction monitoring rules fall into several categories. Here are the most common examples used by financial institutions:
Threshold-Based Rules
- Large cash transactions: Flags transactions exceeding $10,000 in a single day (BSA reporting requirement)
- Cumulative daily limits: Detects when multiple smaller transactions exceed a daily threshold (e.g., $15,000 aggregate)
- Wire transfer limits: Monitors international wire transfers above specific amounts (e.g., $5,000)
Pattern-Based Rules
- Structuring detection: Identifies patterns of transactions just below reporting thresholds (e.g., multiple $9,500 deposits)
- Rapid movement of funds: Detects money deposited and quickly withdrawn or transferred to another account
- Round-tripping: Flags funds transferred out and back within a short timeframe
Geographic and High-Risk Rules
- High-risk jurisdiction monitoring: Tracks transactions to or from countries identified by FATF as high-risk
- Politically exposed persons (PEP): Enhanced monitoring for transactions involving PEPs or their associates
- Watchlist screening: Flags transactions involving individuals or entities on sanctions lists
Behavioral Deviation Rules
- Sudden increase in activity: Detects when transaction volume or value increases significantly from established baseline
- Dormant account activation: Flags previously inactive accounts that suddenly show high-value activity
- Inconsistent business activity: Identifies transactions that don’t align with stated business purpose or customer profile
What Is the Transaction Monitoring Process?
The transaction monitoring process follows a systematic workflow that ensures suspicious activities are identified, investigated, and reported appropriately.
What Are the Key Steps in Transaction Monitoring?
1. Data collection: Transaction data is gathered from various sources including core banking systems, payment processors, and customer information databases
2. Rule application: Automated systems apply pre-configured rules to analyze transactions against established thresholds and patterns
3. Alert generation: When transactions trigger rules, the system generates alerts for compliance team review
4. Investigation: Compliance analysts review alerts to determine if activity is genuinely suspicious or a false positive
5. Decision and action: If deemed suspicious, analysts file a Suspicious Activity Report (SAR) with relevant authorities
6. Documentation: All monitoring activities, decisions, and actions are documented for audit trails and regulatory compliance
This process operates continuously, with real-time monitoring systems analyzing transactions as they occur and post-transaction systems conducting retrospective analysis to catch patterns that emerge over time.
How Does Technology Improve Transaction Monitoring?
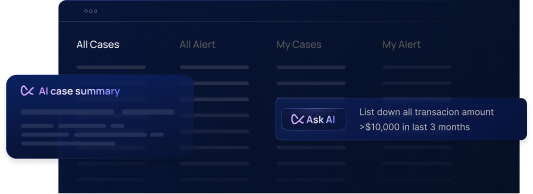
Technology is revolutionizing transaction monitoring. AI and machine learning are transforming how financial institutions detect and prevent financial crimes, offering more scalable, accurate, and efficient solutions than traditional rule-based systems alone.
What Are the Benefits of AI and Machine Learning in Transaction Monitoring?
Automated monitoring processes: AI technologies automate transaction analysis, reducing manual checks and human errors. Systems can process millions of transactions rapidly, identifying the handful requiring further investigation.
Adaptive detection capabilities: Machine learning models learn and evolve from new data and outcomes. Algorithms improve over time at distinguishing between suspicious and legitimate activity, staying ahead of criminals; evolving tactics.
Enhanced risk assessment: AI-powered systems provide deeper risk understanding through granular processing and analysis. This enables more accurate risk evaluations and helps institutions customize monitoring based on specific risk profiles.
Reduced false positives: High false positive rates burden investigation teams and waste resources. AI and machine learning improve detection algorithms, reducing false alarms and letting compliance teams focus on genuine suspicious activities.
Leading providers like Flagright, as a leading provider in AI-native AML compliance solutions, uses this cutting-edge technology to provide robust and dynamic transaction monitoring solutions. These advanced technologies help fintechs and banks improve monitoring processes necessary for strict regulatory compliance and operational integrity.
What Are Best Practices for Implementing Transaction Monitoring Rules?
Successful implementation requires careful planning, stakeholder engagement, and thorough testing. Follow these best practices to ensure your monitoring system works as intended.
How Should You Deploy New Monitoring Rules?
Define clear objectives: Specify what new rules aim to achieve before implementation. Whether reducing false positives, detecting new fraud types, or complying with recent regulatory changes, clear goals facilitate more effective rule development.
Engage stakeholders: Involve departments across your organization—compliance, risk management, IT, and business operations. This collaboration ensures rules are comprehensive and considers multiple perspectives.
Apply risk-based approach: Understand your institutions specific risk exposures and tailor rules accordingly. If wire transfer fraud is increasing, consider tightening related monitoring rules.
Ensure system integration: New rules must integrate smoothly with existing technological infrastructure to prevent disruptions and maximize current data and systems. Check out how we did that for one of the fastest growing fintechs in Europe.
Design for scalability and flexibility: Create rules that can scale and adapt quickly as your organization grows and as criminals modify their tactics.
How Do You Test Transaction Monitoring Rules Effectively?
Conduct pilot testing: Test new rules in a controlled environment before full-scale implementation. This lets you monitor performance and identify issues that aren't obvious during development.
Use simulation and back-testing: Apply new rules to historical data to understand how they would have performed in past situations. Back-testing clarifies potential impact on detecting unusual activity and the frequency of false positives and negatives.
Establish feedback loops: Create mechanisms for testers to provide feedback. Their insights are invaluable for refining rules before broader implementation.
Iterate continuously: Treat implementation as an iterative process. Continuously enhance and modify rules based on testing results. This iterative approach improves monitoring system accuracy and performance.
Maintain compliance documentation: Document all testing procedures thoroughly and ensure compliance with internal and external auditing and regulatory requirements. This documentation is critical for regulatory purposes and future reference.
How Do You Develop Scenarios for Transaction Monitoring?
Transaction monitoring scenarios are specific use cases that define what suspicious activity looks like. Developing effective scenarios requires understanding common money laundering typologies and how they manifest in transaction patterns.
Start with known typologies: Research money laundering methods relevant to your institutions products and customer base. Common scenarios include structuring, layering, integration, and trade-based money laundering.
Analyze historical SAR data: Review past suspicious activity reports to identify patterns and red flags that led to those reports. This historical insight helps build scenarios based on real-world suspicious activity.
Consider product-specific risks: Different products carry different risks. Payment processing has different vulnerabilities than traditional banking. Tailor scenarios to your specific product offerings.
Incorporate regulatory guidance: Use guidance from FinCEN, FATF, and other regulatory bodies on emerging threats and suspicious activity indicators.
Test and refine: Monitor scenario performance continuously. If a scenario generates too many false positives or misses known suspicious activity, adjust parameters or add additional criteria.
Frequently Asked Questions
Can I set up rules to flag high-risk transactions?
Yes. Modern transaction monitoring systems allow you to configure custom rules that flag high-risk transactions based on factors like transaction amount, customer risk rating, geographic location, transaction type, and behavioral patterns. You can set different thresholds for different customer segments—for example, stricter limits for high-risk customers and more relaxed thresholds for established, low-risk customers. The key is balancing comprehensive monitoring with manageable alert volumes.
What is the extent of transaction monitoring depends on?
The extent of transaction monitoring depends on several key factors: customer risk profile (high-risk customers require more intensive monitoring), business model and product offerings, regulatory requirements in your jurisdiction, transaction volume and complexity, and available resources. Financial institutions use risk-based approaches to allocate monitoring resources where they are most needed, ensuring high-risk activities receive appropriate scrutiny while managing operational costs.
How do transaction monitoring procedures work in banks?
Banks use automated systems that continuously analyze transactions against pre-defined rules and machine learning algorithms. The process begins with data collection from core banking systems. Automated rules then screen each transaction for suspicious patterns. When a transaction triggers a rule, the system generates an alert for compliance analysts to review. Analysts investigate alerts, gathering additional context about the customer and transaction. If the activity appears genuinely suspicious, analysts file a Suspicious Activity Report (SAR) with regulators. All decisions are documented for audit trails.
What are AML transaction monitoring best practices?
Best practices include: implementing a risk-based approach that tailors monitoring intensity to customer risk levels; regularly reviewing and updating rules to address emerging threats; minimizing false positives through AI and machine learning; ensuring proper integration between monitoring systems and other AML components like knowing your customer (KYC); providing comprehensive training for compliance teams; documenting all monitoring activities and decisions; conducting regular testing and validation of monitoring effectiveness; and staying current with regulatory guidance and industry developments.
How does payment transaction monitoring differ from traditional banking?
Payment transaction monitoring focuses on higher volumes of smaller transactions, often processed in real-time. Payment processors must monitor for transaction laundering (merchants processing payments for unauthorized businesses), velocity abuse (rapid-fire transactions), and card testing schemes. Traditional banking monitoring typically handles lower volumes of larger transactions with more customer context available. Payment monitoring requires faster decision-making capabilities and specialized rules for e-commerce and digital payment patterns, while banking monitoring can leverage deeper customer relationships and account history.
Why is transaction monitoring important for fintech companies?
Fintechs face unique risks from rapid growth, digital-first business models, and evolving regulatory expectations. Effective transaction monitoring protects fintechs from being exploited by money launderers who specifically target newer, technology-focused companies they perceive as having weaker controls. Beyond compliance, monitoring helps fintechs understand customer behavior, detect fraud, manage operational risk, and build trust with regulators and financial partners. As fintechs scale, robust monitoring becomes essential for maintaining licenses and partnerships with traditional financial institutions.
What are the key components of an effective transaction monitoring system?
An effective system includes: comprehensive data aggregation from all transaction sources; flexible rule engine that supports both threshold-based and pattern-based detection; machine learning capabilities for adaptive threat detection; risk-based customer segmentation; alert management and case tracking workflow; investigation tools with access to customer profiles and transaction history; reporting capabilities for SAR filing and regulatory reporting; audit trail documentation; performance monitoring and tuning capabilities; and integration with other AML components like sanctions screening and KYC.
How often should transaction monitoring rules be reviewed and updated?
Review transaction monitoring rules at least quarterly, with comprehensive annual assessments. More frequent reviews may be necessary when: regulatory requirements change, new products or services launch, significant changes in customer base occur, false positive rate spike, or new money laundering typologies emerge. Additionally, conduct ad-hoc reviews after receiving regulatory feedback or when monitoring effectiveness metrics suggest rules are not performing as intended. Continuous monitoring of key performance indicators helps identify when rule adjustments are needed between scheduled reviews.
What is the difference between real-time and post-transaction monitoring?
Real-time monitoring analyzes transactions as they occur, allowing immediate action to block or delay suspicious transactions before completion. It's particularly valuable for fraud prevention and high-risk scenarios. Post-transaction monitoring reviews completed transactions retrospectively, identifying patterns and relationships that emerge over time. Most institutions use both approaches: real-time for immediate threats and high-risk indicators, post-transaction for pattern analysis and relationship mapping. The combination provides comprehensive coverage while balancing operational efficiency and customer experience.
How do you reduce false positives in transaction monitoring?
Reduce false positives by: implementing machine learning that learns from historical alert outcomes; using behavioral baselines that understand normal activity for each customer; segmenting customers by risk scoring with appropriate thresholds for each segment; refining rule parameters based on performance data; combining multiple indicators rather than triggering on single factors; incorporating contextual data like customer occupation and transaction purpose; regularly calibrating rules using back-testing; and establishing feedback loops where investigators can flag rules generating excessive false positives for tuning.
Practical Tips for Transaction Monitoring Success
Start with regulatory requirements first: Before building custom rules, ensure you meet all mandatory regulatory requirements for your jurisdiction. Compliance is non-negotiable; optimization comes second.
Document everything: Maintain detailed documentation of rule development rationale, testing results, and tuning decisions. This documentation is invaluable during regulatory examinations and helps new team members understand your monitoring approach.
Monitor your monitoring: Track key performance indicators like alert volumes, false positive rates, investigation times, and SAR filing rates. These metrics help you identify when rules need adjustment before problems escalate.
Invest in training: Ensure compliance analysts understand both the technical aspects of your monitoring system and the underlying money laundering typologies. Well-trained teams make better alert disposition decisions.
Don't set and forget: Transaction monitoring requires ongoing attention. Criminals adapt their tactics, regulations evolve, and your business changes. Rules that worked six months ago may need adjustment today.
Use peer review: When developing new rules or scenarios, have multiple team members review the logic and parameters. Fresh perspectives catch issues that the rule developer might miss.
Consider the customer experience: While compliance is critical, overly aggressive monitoring that blocks legitimate transactions damages customer relationships. Balance security with usability, especially for real-time monitoring that can stop transactions in progress.
Taking Action: Building Your Transaction Monitoring Program
Robust transaction monitoring is a crucial means for preventing financial crime and maintaining regulatory compliance. It plays a crucial role in detecting and preventing financial crimes while protecting your institution from compliance failures and reputational damage.
Financial institutions must proactively manage their transaction monitoring systems, regularly updating them to address new threats and regulatory changes. This proactive approach ensures your systems remain compliant and robust enough to handle evolving financial crimes.
The complexity of modern financial crime demands sophisticated monitoring solutions. Traditional rule-based systems alone are no longer sufficient—institutions need AI-powered platforms that can adapt to emerging threats while managing false positive rates effectively.
For institutions looking to enhance transaction monitoring, Flagright offers AI-native AML compliance solutions with built-in AI forensics, tailored to your specific needs. Contact us for a free demo to learn how we can help you optimize your systems for greater effectiveness and compliance. Stay proactive and ensure your transaction monitoring system is a key factor in your operational success.




.svg)






.webp)