Online payments are by far the most popular form of payment today. According to a study by Experian, over 90% of consumers worldwide rely on online payments for purchasing goods and services. However, this increase in online payments has increased payment fraud.
When faced with increasingly secure fraud-protection systems implemented by much larger businesses, fraudsters begin to target smaller, less-secured firms to try their luck. However, there are ways to protect your small business from these fraudulent attacks.
Customers have to believe that their money is safe. But one of the hardest things about spotting and stopping payment fraud is the complexity of the interconnected networks that underpin it.
In this article, we’ll highlight some of the avenues through which these fraudsters can attack you and what you can do to mitigate their impact on your financial institutions.
What is payment fraud?
Payment fraud occurs when someone steals another person’s payment information and uses it to make unauthorized transactions or purchases. The actual cardholder or owner will notice that some trades are being authorized from their card and immediately raise a dispute.
Fraud issue arises for business owners, as they will have to settle the dispute, pay numerous penalties such as chargeback fees and investigation fees, and face an overall loss of time and resources.
In some cases, customers themselves can falsely initiate a chargeback, denying ever having received the product, which is also a form of payment fraud.
With the risk of cybercrime going up, it's important to take a proactive, coordinated approach to stop payment and transaction fraud, since attacks can come from anywhere.
But how do you know when it's happening? How can you spot unusual activity that may signal fraud, and how certain are you that you know your clients' identities?
Types of payment fraud
There are many types of payment fraud/transaction fraud, including:
- Phishing: is a type of cybercrime in which victims are contacted by email, telephone, or text message by an attacker posing as a trustworthy entity in order to obtain sensitive information or data, such as login credentials, credit card details, or other personally identifiable information.
- Identity theft: occurs when someone uses another person's personal identifying information, like their name, identification number, or credit card number, without their permission, to commit fraud or other crimes.
- Malware: any intrusive software developed by cybercriminals (often called “hackers”) to steal data and damage or destroy computers and computer systems.
- Debit card fraud: is when someone steals both your personal identification number ( PIN ) and debit card or debit card information and uses it without your permission to: withdraw cash from an automated teller machine ( ATM ) and make purchases in stores. make purchases online.
- Money mule: someone who transfers or moves illegally acquired money on behalf of someone else.
In the UK, authorized push payment (APP) fraud rose by 71% during the first half of 2021, with the amount taken exceeding card fraud losses for the first time. With APP fraud, a customer gets tricked into authorizing a payment to an account controlled by a criminal or handing over personal details and passwords through tactics such as scam phone calls, text messages, and emails, fake websites, and social media posts.
- Refund fraud or double dipping: An increasingly common type of attack, where the buyer claims that they never received the goods they ordered and wants a refund from your customer service. They will use the money to buy a new item or might even be offered a replacement product, while they sell the original.
- Triangulation fraud: a more complex type of fraud where the criminal will set up a web store or list items on big marketplaces at unrealistic discounts. When they receive an order for an item, they will use the unsuspecting customer’s information as well as the shipping address and a stolen credit card to purchase that item from a different store, pocketing the fees paid to them.
- APT: one of the most lucrative types of payment fraud is the Advanced Persistent Threat (APT), which uses sophisticated hacking techniques to gain unauthorized access to computer networks to steal data.
APTs are often state-sponsored and, according to the European Payments Council (EPC), “must be considered potentially high risk not only for payment infrastructures but also for all network-related payment ecosystems.”
- DDOS: (Distributed Denial of Service) is a form of online payment fraud in which criminals aim to make machines or networks unavailable to users to disrupt services, often through botnets (hijacked computer networks controlled by a hacker). The number of (D)DoS attacks remains high, and the EPC warns of systematic targeting of the financial sector.
How to prevent payment fraud
- Social media lookup: We can see if the cardholder’s details match those of the online social media profile. It helps extract extra info such as a profile picture, full name, bio, etc.
- IP analysis: Beyond checking geolocation, you can also tell if your user is hiding their connection behind a VPN, proxy, or emulator.
- Email analysis: Even a single data point such as a phone number or email address can reveal a trove of data. Was it created from a suspicious domain (free or disposable address)? How hard was the authentication process? Has it appeared in any data breaches? Find out more about reverse email search lookup modules here.
- Phone analysis: Likewise, a phone number can be checked against a record to get a clearer idea of who you’re dealing with. Is it a landline or mobile? Is the carrier’s location close to the shipping address? Is your user relying on a disposable phone number?
All these extra data points will help you connect the user with the credit card information and make a more intelligent decision when accepting or rejecting a purchase.
Choosing a payment fraud prevention solution
A risk-based approach built around customer profiles, security, and payment flows, is key to a robust payment fraud risk-mitigation program – alongside employee and customer awareness of red flags.
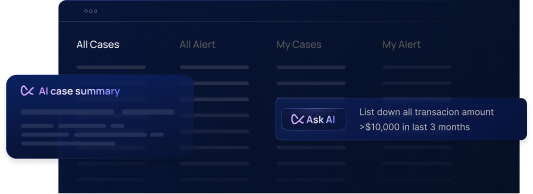
Real-time transaction monitoring, KYC (know your customer), CDD (customer due diligence), dynamic customer risk scoring, blockchain analytics, and sanctions screening; are all solutions Flagright offers, that can help financial institutions better understand their customers, but managing payment fraud risks needs to take place at every stage of the customer journey and throughout firms’ functions, from back-end to customer-facing.
Online payment fraud, in particular, is dynamic and will keep changing as criminals access new technology and techniques to circumvent controls – and financial institutions need to be able to detect changing tactics.
In conclusion
Check out our article on 20 myths about fraud prevention.
Payment fraud can hurt both you and your customers. By aggressively protecting your financial institution against fraud, you can improve your reputation and your bottom line.
The good news is that fraud prevention software has advanced rapidly over the years. You now have more options for integration, pricing models, and mitigating risk.
Contact us here to schedule a free demo.




.svg)