AT A GLANCE
Financial institutions handle massive volumes of sensitive customer data—from account numbers and transaction histories to Social Security numbers and personally identifiable information (PII). This data faces constant threats from cybercriminals through hacking, phishing, ransomware, and insider breaches. Banks and fintech companies protect customer information through multi-layered security including encryption (AES-256), multi-factor authentication, role-based access controls, regular security audits, and compliance with regulations like GDPR, PCI DSS, and GLBA. Effective data security requires combining advanced technologies with employee training and strict policies to prevent financial losses, reputational damage, and regulatory penalties.
Why Do Financial Institutions Need to Know Your Personal Information?
Financial institutions collect and store personal information for four critical reasons: regulatory compliance, fraud prevention, service personalization, and risk management.
Regulatory Compliance: Banks must comply with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations mandated worldwide. These laws require identity verification, transaction monitoring for suspicious activity, and reporting potential financial crimes. Without collecting personal information—names, addresses, Social Security numbers, and identification documents—banks cannot legally open accounts or process transactions. Non-compliance, including failures related to money laundering prevention, can result in fines reaching millions of dollars and the potential loss of banking licenses
Fraud Prevention: Personal information enables financial institutions, brokerages and trusts to establish baseline behavior patterns for each customer. When unusual activity occurs—transactions from unfamiliar locations, sudden large withdrawals, or purchases inconsistent with normal spending—security systems flag these anomalies. If your card suddenly shows purchases in another country while you’re at home, the bank’s fraud detection systems can immediately block the transaction, preventing fraud before any damage occurs.
Service Personalization: Banks use customer data to tailor financial products to individual needs. Transaction histories reveal spending patterns, income stability, and financial goals, helping institutions recommend appropriate credit cards, loans, investments, and savings accounts.
Risk Assessment: Financial details determine creditworthiness and loan eligibility. Banks analyze income, employment history, existing debts, and payment patterns to assess lending risk, protecting both the institution and borrowers from unsustainable debt.
What Are the Main Threats to Customer Data in Financial Services?
Customer data faces threats from external cyberattacks, internal breaches, and third-party vulnerabilities.
External Cyber Threats
Hacking and System Intrusions: Cybercriminals use brute force attacks, SQL injection, and DDoS attacks to breach financial systems. These attacks can compromise millions of customer records in a single breach.
Phishing and Social Engineering: Phishing attacks trick individuals into revealing sensitive information through fraudulent emails, messages, or fake websites that appear authentic. Spear-phishing targets specific individuals with personalized messages, making detection extremely difficult.
Ransomware Attacks: Ransomware encrypts an institution's data, demanding payment for decryption. If institutions refuse, attackers may delete data, sell it, or release it publicly—causing catastrophic damage to customer trust.
Malware and Trojans: Malicious software infiltrates systems through infected emails or compromised websites. Once inside, malware logs keystrokes, screenshots information, or provides remote access to attackers.
Insider Threats
Malicious Insiders: Disgruntled employees with system access can steal customer data for personal gain. A database administrator could extract thousands of customer records and sell them on dark web markets.
Negligent Employees: Human error causes significant breaches. Employees might accidentally email customer information to wrong recipients, misconfigure security settings, click malicious links, or use weak passwords.
Compromised Credentials: If employees use the same password across platforms, a breach on an unrelated website could expose their banking system credentials.
Third-Party Vendor Risks
Financial institutions rely on cloud service providers, IT consultants, payment processors, remittances services, and supply chain partners. Each vendor with system access creates potential vulnerability. The 2013 Target breach, exposing 40 million credit card numbers, occurred through a third-party HVAC vendor's compromised credentials.
How Do Banks Typically Secure Sensitive Client Information?
Banks protect customer information through layered security strategies combining technology, policies, and awareness.
Data Encryption Standards
Encryption at Rest: Data stored in databases receives encryption protection using Advanced Encryption Standard (AES-256)—the same standard used by governments for classified information. Customer accounts, transactions, and personal information remain encrypted in storage.
Encryption in Transit: When data travels across networks—during online banking, mobile transactions, or ATM communications—Transport Layer Security (TLS) protocols encrypt the transmission, preventing interception attacks.
Multi-Factor Authentication (MFA)
MFA requires multiple forms of identity verification before accessing accounts. Modern banking combines passwords (something you know), codes sent to phones (something you have), and fingerprint verification (something you are). Even if attackers steal passwords, they cannot access accounts without also having physical devices and biometric data.
Access Control Systems
Role-Based Access Control (RBAC): Employees receive access rights based on specific roles. A customer service representative views basic account information but cannot access transaction processing systems. This compartmentalization limits damage if credentials become compromised.
Attribute-Based Access Control (ABAC): Sophisticated systems consider factors including access time, location, and data sensitivity. Systems might allow account access only during business hours from approved IP addresses.
Continuous Monitoring and Threat Detection
Security Information and Event Management (SIEM): SIEM systems aggregate data across entire IT infrastructures, analyzing millions of events to detect security incidents. Machine learning establishes normal behavior baselines and alerts teams when deviations occur.
Intrusion Detection and Prevention Systems (IDPS): These monitor network traffic for known attack patterns. IDPS can automatically block malicious traffic, quarantine affected systems, and alert security personnel.
What Compliance Regulations Govern Financial Data Security?
Financial institutions must navigate complex regulatory frameworks mandating specific data protection standards.
General Data Protection Regulation (GDPR)
General data protection regulation (GDPR) affects any organization handling EU citizens' personal data. Key requirements include data minimization, explicit consent, right to deletion, 72-hour breach notification, and appointing Data Protection Officers. Penalties reach €20 million or 4% of annual global revenue (whichever is higher).
Payment Card Industry Data Security Standard (PCI DSS)
The payment card industry data security standard (PCI DSS) applies to all organizations storing, processing, or transmitting credit card information. Requirements include maintaining firewalls, encrypting cardholder data, using antivirus software, restricting access by business need, tracking all access, and regularly testing security systems. Non-compliance results in fines and potential inability to process card payments.
California Consumer Privacy Act (CCPA)
The California consumer privacy act (CCPA) grants California residents rights to know what data is collected, delete personal information, opt-out of data sales, and receive equal service regardless of exercising privacy rights.
Gramm-Leach-Bliley Act (GLBA)
The gramm-leach-bliley act (GLBA) requires U.S. financial institutions to disclose information-sharing practices and protect customer data through comprehensive security programs, risk assessments, and regular testing.
Basel committee on banking supervision (BCBS) 239
Although Basel committee on banking supervision (BCBS) 239 isn't exclusively about data protection, it highlights the need for effective risk data aggregation and reporting. It indirectly demands robust data management and security processes by requiring banks to maintain accurate and timely risk data.
Sarbanes-Oxley Act (SOX)
Sarbanes-oxley act (SOX) mandates internal controls for corporate disclosures, including data security measures. Public financial institutions must establish controls ensuring confidentiality, integrity, and availability of customer data with detailed logging and auditing capabilities.
What Security Tools Do Financial Institutions Use?
Modern financial institutions deploy sophisticated security technologies creating multiple defense layers.
Firewalls: Act as barriers between trusted internal networks and untrusted external networks, examining all traffic and blocking threats based on security rules.
Intrusion Detection and Prevention Systems: Monitor network traffic for malicious activity and automatically block suspicious traffic or quarantine affected systems.
Data Loss Prevention (DLP): Prevent unauthorized transmission of sensitive data by monitoring information in use, in motion, and at rest. DLP blocks attempts to email customer data externally or upload files to unauthorized cloud services.
Identity and Access Management (IAM): Manage user identities and access privileges, ensuring only authorized individuals access specific data. Features include single sign-on, multi-factor authentication, and privileged access management.
Endpoint Security Platforms: Protect laptops, smartphones, and tablets from malware, unauthorized access, and data theft through antivirus protection, device encryption, and mobile device management.
Cloud Security Tools: Protect data in cloud environments through Cloud Access Security Brokers (CASB), cloud workload protection, and cloud data encryption.
SIEM Systems: Aggregate and analyze data from across IT infrastructure, providing real-time security alerts, compliance reporting, and forensic investigation capabilities.
How Can Financial Institutions Protect Against Insider Threats?
Principle of Least Privilege
Grant employees minimum access necessary for job functions. A teller needs balance information but not loan approval authority. Regularly review access rights as roles change.
User Behavior Analytics (UBA)
UBA systems establish normal behavior baselines for each employee. When behavior deviates—accessing unusual databases, downloading large files, logging in at odd hours—systems alert security teams.
Separation of Duties
Critical operations require multiple people. Initiating large transfers might require one employee to create the transaction and a supervisor to approve it.
Comprehensive Audit Trails
Log all data access with detailed records: who accessed what information, when, from where, and what actions they performed. Audit trails enable forensic investigations and deter misconduct.
Exit Procedures
When employees leave, immediately revoke all system access, disable credentials, collect company devices, and change shared passwords. Monitor former employees' activities for unusual patterns.
What Are Best Practices for Securing Financial Data?
Develop Comprehensive Security Policies: Document clear policies covering acceptable use, password requirements, data classification, incident response, and vendor management.
Implement Zero Trust Security: Assume any device, user, or network could be compromised. Every access request requires verification regardless of source.
Conduct Regular Vulnerability Assessments: Continuously scan systems for security weaknesses—unpatched software, misconfigured settings, weak passwords, or vulnerable applications.
Establish Incident Response Plans: Prepare detailed procedures for detection, containment, investigation, notification, recovery, and post-incident review.
Practice Defense in Depth: Layer multiple security controls so if one fails, others provide continued protection.
Encrypt Data Everywhere: Apply encryption to data at rest, in transit, and in use throughout its lifecycle.
Manage Third-Party Relationships: Vet vendors thoroughly, require security certifications (ISO 27001, SOC 2), and regularly audit compliance.
Foster Security-Aware Culture: Make security everyone's responsibility through leadership prioritization, adequate resource allocation, and celebration of employees who identify issues.
What Future Trends Are Shaping Financial Data Security?
Artificial Intelligence and Machine Learning: AI analyzes vast data volumes identifying patterns humans cannot perceive, enabling real-time automated threat responses.
Quantum Computing: While quantum computers could break current encryption, they also enable quantum encryption methods providing unprecedented security. Institutions must prepare for post-quantum cryptography.
Privacy-Enhancing Computation: Federated learning, differential privacy, and homomorphic encryption enable data analysis without exposing underlying information.
Zero Trust Network Access (ZTNA): Provides granular, application-level access based on identity verification and device security posture rather than broad network access.
Blockchain Technology: Blockchain’s decentralized and immutable nature offers advantages for crypto and stablecoin ecosystems, including identity verification, secure transactions, and ensuring data integrity.
Advanced Biometric Authentication: Behavioral biometrics analyzing typing patterns, mouse movements, and voice characteristics provide continuous authentication throughout sessions.
Frequently Asked Questions
Why is safeguarding PCI data essential in financial transactions?
PCI data protection prevents fraud, protects customers from identity theft, maintains payment processing capabilities, and avoids severe penalties ($5,000-$100,000 monthly fines). Breaches destroy trust and expose customers to identity theft.
How do online banks ensure customer data safety for high-yield accounts?
Online banks use bank-grade encryption (AES-256), multi-factor authentication, continuous monitoring, FDIC insurance, secure login procedures, automated fraud detection, and regulatory compliance. Many implement biometric authentication and real-time alerts.
How can institutions protect sensitive data while testing new applications?
Institutions use data masking, synthetic data generation, test environment isolation, limited access controls, and strict data retention policies. Production data should never enter test environments without proper sanitization.
What measures do financial advisory firms take to protect client data?
Advisory firms implement encrypted client portals, secure document storage, role-based access controls, security training, privacy agreements, secure communications, periodic audits, cyber insurance, and SEC compliance.
What security features protect sensitive financial reports?
Reports receive protection through encryption, access logging, watermarking, digital rights management, version control, secure distribution channels, expiring access links, and password protection.
How do expense tracking apps prioritize data security?
Expense apps use read-only bank connections, bank-level encryption, two-factor authentication, secure credential storage, automated logout, and regular security audits. Reputable apps never store actual bank credentials.
What are security considerations in financial data sharing?
Data sharing requires informed consent, purpose limitation, encryption during transmission, data minimization, access controls, audit trails, regulatory compliance, clear privacy policies, and secure API connections.
Key Security Recommendations
For Financial Institutions:
- Implement defense-in-depth with multiple security layers
- Conduct quarterly security assessments and penetration testing
- Maintain comprehensive employee training with phishing simulations
- Deploy AI-powered threat detection and monitoring
- Establish Zero Trust architecture
- Encrypt all sensitive data
- Vet third-party vendors thoroughly
- Foster security-conscious organizational culture
For Customers:
- Enable multi-factor authentication on all accounts
- Use strong, unique passwords for each institution
- Monitor account activity daily
- Be skeptical of unexpected communications
- Never share passwords, PINs, or one-time codes
- Use secure networks for transactions
- Keep devices updated with latest security patches
- Report suspicious activity immediately
The digital transformation of financial services has created unprecedented convenience while introducing significant security challenges. Financial institutions bear fundamental responsibility to protect customer data through comprehensive security programs combining advanced technologies, rigorous policies, regulatory compliance, and security-aware cultures.
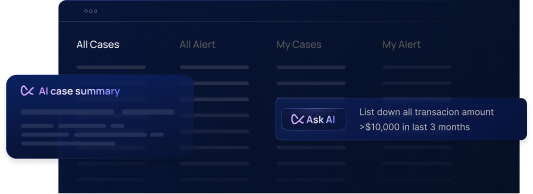
Platforms like Flagright provide a no-code, centralized AML compliance and fraud prevention platform, offering real-time transaction monitoring, customer risk assessment, sanctions screening, identity verification, AI Forensics, and case management, all integrable within one week.
Protecting customer data isn't just about regulatory compliance—it's about honoring the trust customers place in financial institutions to safeguard their most sensitive information.
Flagright also offers fintech licensing and advisory services, helping you navigate the complexities of the fintech regulatory landscape. One of the standout features of Flagright is its speed of integration. Flagright wraps up integrations within one week, which means your institution can start benefiting from enhanced data security in no time. Schedule a free demo with us to get started.




.svg)






.webp)